Podcast: Play in new window | Download (Duration: 27:07 — 31.0MB) | Embed
In this Spotlight Podcast, sponsored by Synopsys: In the wake of a presentation at Black Hat about security flaws in implantable pace maker devices, Synopsys Principal Consultant Dan Lyon joins us to talk about why medical device makers struggle to make their connected medical devices more secure. Dan and I discuss some of the flaws in the approach that medical device makers take to security, and how manufacturers can take a page out of their own book: applying the same standards to cyber security as they do to – say- device safety.
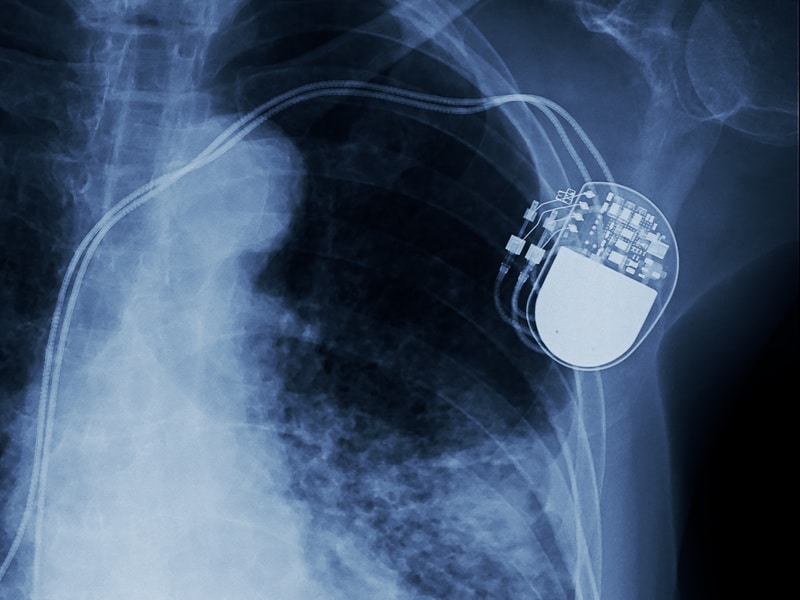
The security of medical devices figured prominently at last week’s Black Hat, B-Sides and DEF CON hacking conferences in Las Vegas. In one of the more news-worthy demonstrations, researchers Billy Rios and Jonathan Butts demonstrated how to remotely exploit an implantable pacemaker made by the firm Medtronic, showing how malicious software could be used to take control of the device – even executing shocks to a patients.

This wasn’t the first demonstration of its type. Rios and Butts have been publicly butting heads with Medtronic for months over the security flaws he found. At Black Hat, he characterized the ponderous process of working with the firm on fixes as “an 18-month roller coaster of unresponsiveness, technical inefficiencies and misleading reactions.” And, of course, hacks and security flaws in implantable devices are not new. The late, great device hacker Barnaby Jack demonstrated an over the air attack on an insulin pump at a hacker conference in Miami way back in 2011.

The question is this: why is it that sophisticated, multi national firms that make medical devices have such a hard time addressing cyber risk in their products? How is it that a manufacturer can possess the design savvy to make an electronic device that lives within the human body, yet fail utterly to understand and account for the possibility of even trivial electronic manipulation and attacks?
[You might also be interested in:Spotlight: Deepika Chauhan of Digicert on the Challenges of Securing the Internet of Things]
Our guest in this Spotlight podcast knows better than anyone the answer to those questions. Dan Lyon is a principal consultant with Synopsys and a seasoned medical device engineer who spent more than 18 years working as an engineer at medical device maker Medtronic.
In this spotlight conversation, Dan and I talk about the cyber risk and about the many challenges manufacturers have securing connected medical devices from software based attacks. One of the fundamental problems, Lyons tells me, is that medical device makers often focus on a single technology “fix” for cyber security – for example the use of encryption – when they need to take a more holistic approach to securing connected health devices. The job of securing medical devices isn’t akin to plugging a hole in the firewall, Lyons notes. Instead, it is a far bigger job akin to the process of designing medical devices for safety.
“Manufacturers need to take a step back,” he said. “They need to conduct risk management and take a page from their own safety risk management playbook.”
Rather than assuming that all users of a device are authorized users, medical device makers need to begin envisioning users with malicious intent – scheming to attack their device and use it for harm, rather than to successfully deliver patient care.
Check out our full conversation using the link above. You can also listen to our podcast over at Blubrry or on Soundcloud.