Scores of contests at the annual DEF CON event reveal hacker culture in its Baroque glory, with tests of social engineering and IoT hacking skills taking center stage.
They don’t call it “Hacker Summer Camp” for nothing. Attendees to the Black Hat and DEF CON hacker conferences in Las Vegas this week have a dizzying array of contests and games challenging vying for their attention.
This week’s Black Hat, DEF CON and B-Sides events featured scores of competitions as new challenges centered on robotics and artificial intelligence take their place alongside decades old competitions like lock picking and “Hacker Jeopardy.” The events are part of a long history of games, contests and other side events that surround two of the U.S.’s largest gathering of computer hackers and security experts – evidence of hacker culture’s growing reach.
Contests zero in on skills, friction points in community
Contests have long been a way to call out foundational hacking skills such as puzzle solving and cyber forensics. At the Black Hat Briefings, for example, The Crimson Thorn Challenge sponsored by the security firm WatchGuard Technologies challenged contestants to try their hands at a host of problems involving steganography, hashing, packet sniffing, general cyphers, and more. Marc Laliberte, Senior Security Analyst at WatchGuard and CTF veteran who helped design the puzzles, said Crimson Thorn was designed as a “serious challenge for those looking for something serious.” Participants receive a customize-able badge based on the Rasberry Pi and competed for prizes including a JDI Spark Drone, a 3D printer and, of course, the bragging rights.
The purse was considerably richer for those who competed for the GeekPwn contest at DEF CON*: $800,000 in prizes. That included the Robot Agent Challenge, in which contestants needed to use a robot to “place a covert listening device, open a safe to get an information card, open a book to get an information card, [and] plug a malicious USB and keyboard recorder into a computer.”
DEF CONtest: Games and Contests Dominate Annual Gathering
Games, puzzles and contests defined the 26th annual DEF CON with a total of 50 contests will take place from Thursday through Sunday. At the top of the list included the DEF CON badge challenge, centering on solving a complex puzzle embedded in the event’s 8 different flavors of smart badges. The puzzle sent thousands of contestants scrambling to connect their badges with those of other attendees, unlocking features and clues and analyzing the electronic output of the badges and discover clues, hidden features and functionality.
[You might also like: Expert says: Hack your Smart Home to Secure It]
Games and contests often underscore and highlight areas of professional interest or tension within the information security and hacking communities. Social engineering skills such as those that often make up the early stages of cyber attacks, when attackers “phish” unsuspecting individuals were the root of a number of contests, including the Social Engineering Capture the Flag, in which contestants compete to talk their way into getting otherwise sophisticated firms to cough up sensitive information. This year’s DEF CON extends social engineering game play down to young hackers, as well, with a capture the flag event specifically geared to kids.
The Internet of Things figured prominently in games at both Black Hat and DEF CON. Again this year, DEF CON’s ICS Village was filled with teams of hackers crowded around laptops as they try to hack a range of consumer and commercial IoT devices. Contests include SOHOpelessly Broken, a weekend long marathon that has DEF CON attendees sniffing out vulnerabilities in off-the shelf IoT devices like home broadband routers, voice assistants and smart watches.
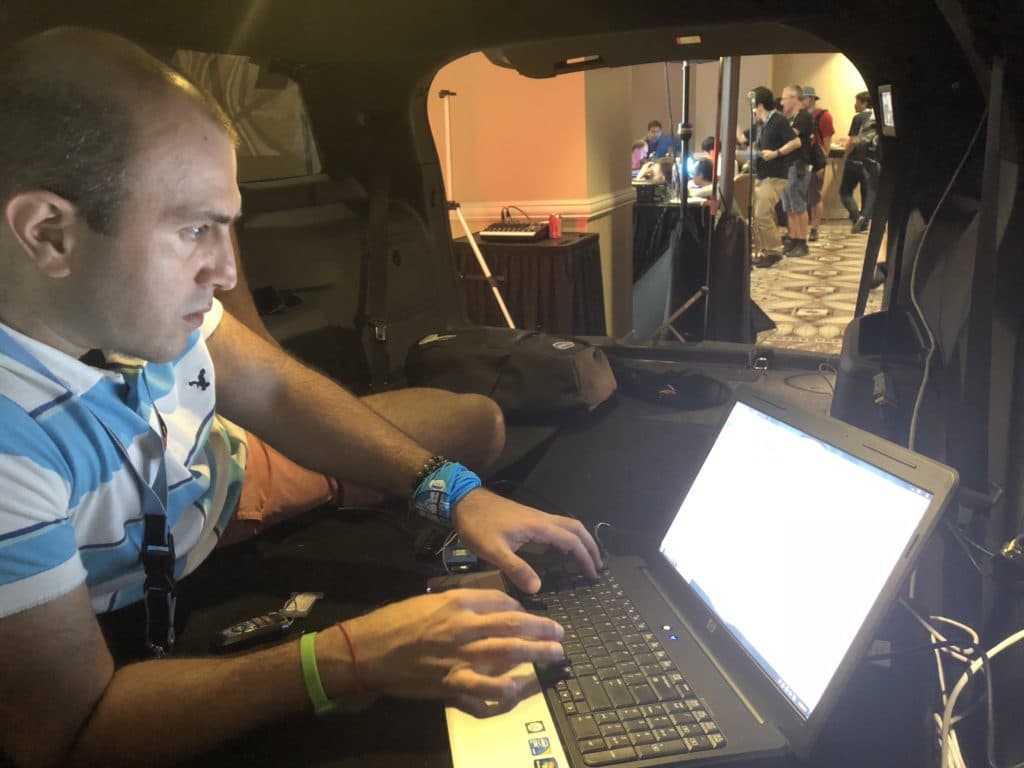
At DEF CON’s Car Hacking Village, hundreds of attendees tried their hand at manipulating the software and hardware that is used to control millions of modern vehicles, like the 2012 Ford Focus. One contest saw DEF CON “goons” (security) throw volunteers in the back of a late model Ford SUV and challenged them to use their hacking skills to spring themselves from the vehicle by unlocking the car and opening the trunk before their time ran out.
[You might also like:Next privacy trap for consumers? Their cars.]
Bryson Bort, the Chairman and Founder of the firm Grimm, which runs the Car Hacking Village, said that his company has built on the Car Hacking Village and now offers a 5 day course to auto industry professionals to help them understand how hackers look at and seek to undermine software based controls in vehicles. Still, the Car Hacking Village was more understanding how the underlying software that runs vehicles can be tweaked to tuning vehicle performance than about launching malicious attacks on vehicles.
Such tinkering and modifications are part and parcel of U.S.’s vibrant car culture, said Tomas Tillery, a security researcher at Grimm and an instructor at the DEF CON Car Hacking Village. “The idea of the guy in his garage tuning up his car? That’s Americana,” he said. “Phones are things people have. Cars are things people own.”
That could change, especially as vehicles become more sensor-rich and network, and as fleets of corporate-owned and operated autonomous vehicles come to replace individually owned vehicles, said Bort.
“If you look at the amount of data available in interconnected cars and the level of connectivity and then how much is going over networks the car manufacturers maintain, there is a question about the privacy of the data,” he said.
That may raise the stakes on events like DEF CON and its various Villages and contests to foster the skills needed for consumers to take ownership of their own data and devices.
Paul Roberts contributed to this article.
(*) Correction: an earlier version of this story mistakenly identified the conference that GeekPwn was part of. The story has been corrected. PFR 8/13/2018.

Very Interesting Article…
I truly appreciate this article post.Really looking forward to read more. Much obliged.
Thanks for the mention. Car Hacking Village is run by Robert Leale (not Grimm). I work hard to organize the event. Grimm is an amazing sponsor and contributor to the village as are many other companies (FCA, VW, Aptiv, Novetta). Check out CarHackingVillage.com or @CarHackVillage to get more information about our locations.