Low-hanging Internet of Things security fruit may be left unpicked, as connected device makers fret about the predation of sophisticated hackers, but balk at simple security fixes, a Security Ledger and LogMeIn survey finds. You can download the full report here in PDF format.
A survey by LogMeIn and The Security Ledger found that IT professionals working at companies developing or producing connected products for the Internet of Things are very concerned about the security of those devices. The problem: their concern is often focused on the wrong set of problems.
Low hanging security fruit may be left unpicked, as connected device makers fret about the predation of sophisticated hackers and supply chain attacks, but balk at simple fixes like strengthening authentication and software update features. That’s one conclusion of a survey of 400 IT professionals that assessed the level of interest in both connected products and device security at firms that make physical products.
Strong momentum towards Internet of Things
On the positive side: the momentum behind connecting products to the fast-growing Internet of Things is very strong, our survey found. Almost a quarter of survey respondents (23%) said they worked for companies that had “already developed and deployed one or more connected products” and more than half (51%) said they worked for companies that were “currently developing one or more connected products.” Just over a quarter (26%) said their company was still in the beginning stages: researching the development of its first connected product or looking to connect existing product(s) to the Internet.
That interest stretches across industries, though industries like consumer electronics, popped out of the survey data as further down the road to connecting products to the Internet of Things. For example: almost a third (30%) of respondents from firms that were in the consumer electronics industry and 27% of those working in the home or business product industry said their employer already had one or more connected products on the market.
What’s driving interest in connected products? The same factors that drive much product development: competition. More than a third of respondents (35%) to our survey cited pressure to differentiate from competitors as the motivation to build a connected product or to add connectivity to an existing product. For many respondents (29%), connecting their product was about improving it. Smaller but meaningful shares of respondents cited the desire to realize new revenue opportunities (17%) or discover revenue opportunities in data collected by smart products (13%).
Security for connected devices a top priority
For these professionals, security was a top (though notably not the top) concern. Asked to rank their priorities in developing a connected product, respondents said that having “the most secure product of its class” was their second most priority, right after having the “best performing” product in its class. That’s an encouraging finding: suggesting that concerns about protecting connected devices from the predation of hackers and other threats are in the forefront within product making firms.
There is reason for concern, though. The Security Ledger/LogMeIn survey found that employees of companies that already had one or more connected products on the market ranked security a notably higher priority than did employees of companies that were still in the early stages of researching a connected product. In fact, close to half (43%) of respondents who worked for companies that had already developed and deployed a connected product ranked security as a top priority. Just 30% of employees who worked for companies that were still researching or developing connected products ranked it that high.
That may suggest that connected product firms are coming around to security as an issue not during the early design and development, but after they have already pushed products to market – far from an ideal scenario.
Misplaced priorities?
There’s also some evidence that companies that are developing connected products are focusing on a set of problems and imagined adversaries that, while not wrong, may be overshadowing bigger threats and problems.
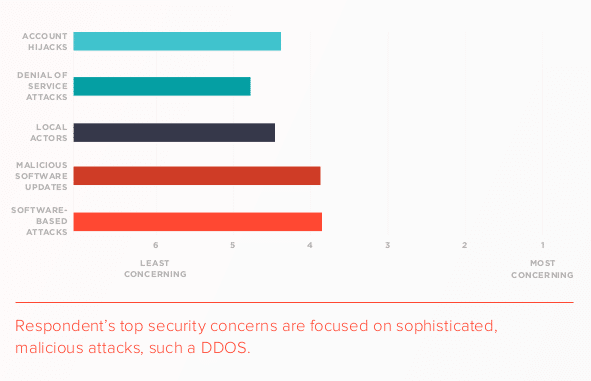
For example, respondents to our survey said that skilled hackers and cyber criminal groups rated as their biggest concerns, topping out common problems like weak communications security and authentication. Unsurprisingly, skilled hackers were seen as a bigger threat than ‘script kiddies’ amongst our respondents, as well. ‘If you’re going to hack our product,’ the respondents seemed to be saying, ‘you better be good.’
Whether that assessment of threat actors is accurate (events like the Mirai and Brickerbot infections suggest that it may not be), our respondents thinking about what attacks were likely to affect their deployed devices is harder to explain. Specifically, the men and women who responded to our poll said that remote, software-based attacks on devices were their biggest concern just ahead of malicious software updates- the kind of supply chain attack the world witnessed with the NotPetya malware outbreak. Those threats may be real, but they out-polled common attacks like account hijacking (the Mirai attack vector) or even denial of service attacks – an endemic online threat that should be a top concern for any connected device maker.
In a similar vein, 0ur respondents considered endemic security problems like weak transport (or communications) security, device impersonation (“spoofing”) and vulnerable mobile applications as comparatively low priorities, even though documented incidents of attacks against connected devices have illustrated that attackers frequently target just such vulnerabilities in connected devices.
Not ready to learn history’s lessons
We saw the same pattern when we asked respondents to talk about possible security remediation. Despite high-profile security events like the NotPetya malware attack in Ukraine that have underscored the risk that vulnerable software supply chains, only a minority of respondents (44%) backed features like restricting customers’ access to firmware updates or cryptographically signing firmware updates (43%).
There’s reason for optimism in our survey. Respondents indicated a strong support for security features like strong second-factor authentication and layered user authorization schemes that limit most users permissions on connected devices. Firms also expressed a willingness to work and partner with third-party providers on some of the more challenging aspects of device deployment (like communications security and user authentication).
Still, the survey should offer caution that far more education and direction is needed within the connected device space, lest device makers leave low hanging security fruit unpicked and leave future IoT deployments vulnerable to attack.
You can download our full report here.
Editor’s note: for this report, LogMeIn Xively contracted with Security Ledger to survey 400 professionals at firms making physical products in industries including consumer electronics, “smart” home, industry and life sciences. Respondents were asked a series of questions both about their employer’s connected product plans and their top concerns on the subject of how to best secure those connected products.

