In-brief: The recently disclosed trove of personnel files by an US Air Force officer is one piece of a much larger phenomenon: exposed, vulnerable and Internet-connected network attached storage (or NAS) devices chock full of gigabytes sensitive data.
The recently disclosed trove of personnel files by an US Air Force officer is just the latest in a string of incidents affecting the military, law enforcement and healthcare sectors. In each, there’s a common culprit: exposed, vulnerable and Internet-connected network attached storage (or NAS) devices chock full of gigabytes sensitive data.
The US Air Force breach is the byproduct of flaws common to consumer-grade NAS devices: vulnerable configurations that give would-be attackers easy access to the drive’s contents. As many as one in every 10 such devices accessible from the Internet is leaking data in a similar fashion, according to researchers at the firm MacKeeper, which discovered the Air Force data.
As reported by ZDNet and MacKeeper Security, the exposed Air Force data included a spreadsheet containing information on open investigations of Air Force Personnel and sensitive links to Department of Defense systems. The data, which belonged to an unnamed Air Force Lieutenant, was backed up to a Network Attached Storage (NAS) device and exposed to the Internet through an insecure rsync port. Rsync is a common utility for transferring and synchronizing files between two computer systems.
Researchers from MacKeeper discovered the device in a routine and automated canvass of the public Internet using the Shodan search engine, Bob Diachenko a spokesman for MacKeeper Security Research Center told The Security Ledger. Such searches turn up tens or hundreds of thousands of NAS devices made by a wide range of firms.
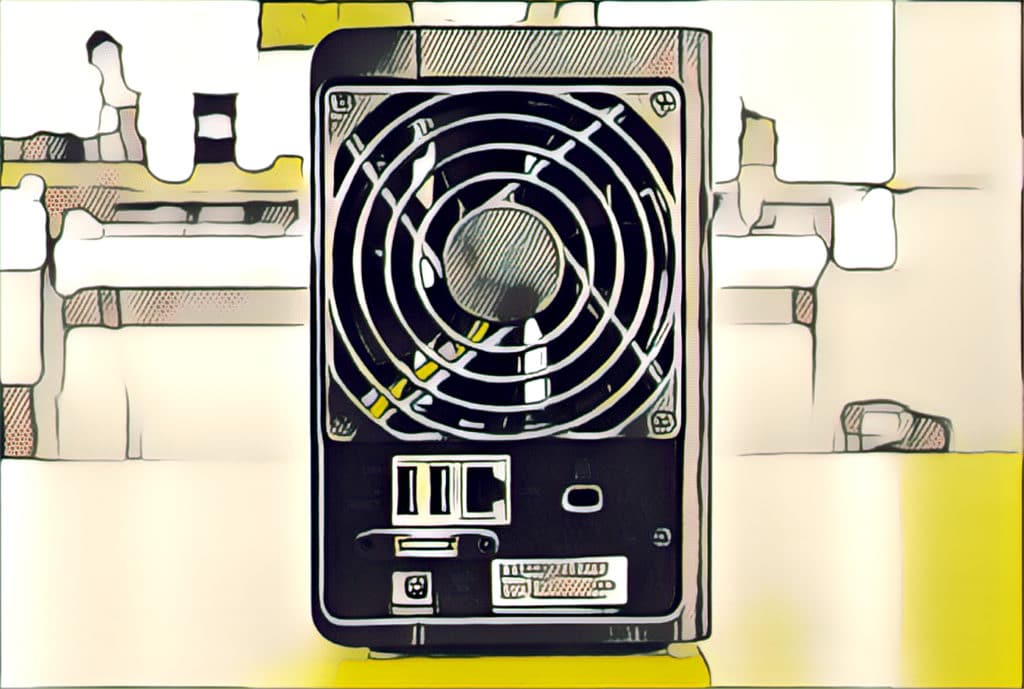
The devices, sold by companies like Seagate, Western Digital, Synology, Buffalo and others have become popular on both business and home networks. They offer a variety of features, from local and cloud-accessible data backup to virtual private networking and video and music streaming. But the devices are prone to the same problems that leave webcams, digital video recorders and other connected stuff vulnerable to attack. Namely: exploitable software holes and weak or default passwords that give remote attackers access to gigabytes or terabytes of sensitive data.
The NAS drive in question was hosted on an IP address belonging to GCI Communications, an US telecommunications firm that operates in the State of Alaska. MacKeeper does not know how long it was exposed to the public.
The company’s researchers have been coordinating with a Special Agent of the Computer Crime Investigative Unit at U.S. Army CID since the breach was disclosed, Dianchenko said. He declined to name the service member involved or comment on the investigation. A spokesman for Army CID referred our inquiry to the US Air Force Office of Special Investigations (OSI). Calls and email messages to OSI were not returned prior to publication.
After helping to discover the data trove, MacKeeper researcher Chris Vickery used personal contacts to notify the US Air Force about the existence of the exposed drive and to get the data taken offline – a process that took “several hours,” Dianchenko. MacKeeper said the data obtained from the drive “will be safely and securely wiped as soon as requested by the USAF.” “It is hard to tell how many other devices remain open and accessible,” Dianchenko wrote. “Our discovery will most likely effect major changes in the way the Military lets officers store data on NAS devices,” he said.
The incident has exposed a serious hole in the U.S. Military’s defenses as well as those of private firms: insecure Internet connected storage and backup devices that are deployed in workplaces and on employees’ home networks. NAS devices vacuum up sensitive data from company owned devices as part of scheduled or user-initiated data back ups.
In just one recent example, researchers from MacKeeper discovered data from the Warren County, Missouri, Sherrif’s Department backed up to an insecure backup device. The leaked data included audio recordings containing police interviews with confidential informants and witnesses as well as crime scene photos, according to this report. MacKeeper researchers discovered the data and reported it to Warren County in January.
A vulnerable NAS device was also the source of a data breach at Potomac Healthcare Solutions, a health provider that serves the US Government including the US Military’s Special Operations Command (SOCOM) through a relationship with government contractor Booz Allen Hamilton. In December, 11 gigabytes of sensitive information from Potomac was found exposed to the public Internet via an unprotected NAS device attached to a Potomac Healthcare IP address.
A search of the public Internet for common NAS devices using the Shodan search engine reveals tens of thousands of devices with public Internet addresses. MacKeeper estimates that about 10% of those are mis-configured – typically able to be accessed without a password using the rsync protocol on port 873. That’s the same vulnerability that exposed the Air Force data, Dianchenko said. As a result, the problem is likely to extend well beyond the Air Force, affecting personnel in other branches of the military, as well as the civilian government and private sector firms, as well.
“NAS devices are full of unstructured and human generated data that are at risk of falling into the wrong hands,” said Adam Rosen, the Vice President of Data Access Governance at the firm STEALTHbits.
Companies frequently give employees too-liberal access to sensitive data. That data ends up on their work device and, by way of “shadow” IT like cloud based backup services and home NAS devices, it ends up slipping from the company’s control. The leaks are unintentional, but still damaging, he said.
“Inadvertent mishandling of sensitive information is one of the most common things we encounter,” Rosen told The Security Ledger. “Most organizations do not have right controls in place. We see this all the time — more than we should.”


Pingback: Episode 22 | March 26, 2017 – Craig Smith