In-brief:The security firm Symantec said it is investigating a string of cyber attacks in the Middle East linked to Shamoon, a piece of destructive malicious software linked to the government of Iran.
The security firm Symantec said it is investigating a string of cyber attacks in the Middle East linked to Shamoon, a piece of destructive malicious software that is believed to be linked to the government of Iran.
Symantec said that new attacks may be linked to the doings of a group it calls the “Greenbug network spy gang.” The report comes as at least one prominent Saudi chemical firm, Sadara, said on Monday that it was experiencing a “network disruption” and was working to resolve it.
Sadara, which is a joint venture between the Saudi Arabian Oil Company and Dow Chemical Co. of Michigan said via its Twitter account that it had stopped “all network-related services” as a precaution.
[See also: “In Iran, New Data Wiping Malware on the loose.“]
A report from Reuters cited state-run Saudi television said that government agencies and private institutions were hit with the Shamoon virus, including the Saudi Labor Ministry. The ministry said it was working with the Interior Ministry to contain the virus. Other reports put said as many as 15 private and public sector organizations had been hit.
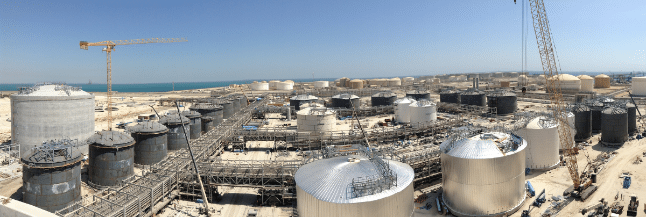
Shamoon first came to light in attacks on oil firms in 2012 including RasGas and Saudi Aramco. The malware is destructive: wiping out the hard drive of computers it infects and displaying a message for victims.
After going dormant, it resurfaced in December, little changed in 4 years, but with a picture of the body of Alan Kurdi, a three year-old Syrian refugee to who drowned trying to cross from Turkey to Greece with his family. Government agencies were the target in the December attack, as well.
Symantec said the latest attack targeted a number of institutions in the Middle East, including in the aviation, energy, government, investment and education sectors. And, rather than just wiping the hard drives of victims, the latest Shamoon variant uses a Trojan horse program, Ismdoor to steal data from its victims.
The security firm said that use of the Ismdoor Trojan is associated with a state-linked hacking group it calls “Greenbug” and that the Trojan has been used against a number of targets in a wide range of sectors across the Middle East in the last six months.
“As part of the operation, legitimate infrastructure belonging to an organization in the energy sector was used to host the Ismdoor payload,” Symantec said it a post on the company’s research blog. In addition to Saudi Arabia, Iran, Bahrain, Iraq, Qatar, Kuwait, and Turkey were victims of attacks. A Saudi organization in Australia was also targeted.
The attacks begin with phishing email attacks containing a malicious attachment designed to look like a business proposal. It isn’t clear whether the deployment of the Shamoon wiper malware is also the work of the Greenbug group, but Symantec said there are coincidences between the use of the Shamoon wiper malware and the activity of the Greenbug group that are difficult to explain otherwise.
