
In-brief: Research from the firm IOActive has discovered exploitable holes in in-flight entertainment software from the firm Panasonic Avionics that may make planes vulnerable to hacking and manipulation. Editor’s note: updated with comments from interview with Ruben Santamarta of IOActive. PFR 12/21/2016
Research from the firm IOActive has discovered exploitable holes in in-flight entertainment software from the firm Panasonic Avionics that may make planes vulnerable to hacking and manipulation.
IOActive researcher Ruben Santamarta on Tuesday said his investigation into Panasonic Avionics inflight entertainment (or IFE) software found vulnerabilities that could allow an attacker to compromise systems that cabin crew use to communicate with passengers. Given the vulnerabilities he discovered, Santamarta said the possibility also exists for skilled attackers to use vulnerabilities in flight entertainment systems to pivot to other, higher value in-flight systems, though he found no proof that such attacks were possible.
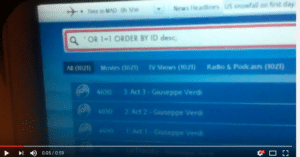
Santamarta documented a range of flaws in the IFE software including vulnerability to SQL injection attacks, the ability to access arbitrary files and a flaw that could enable a passenger to bypass a credit card check. A video posted on YouTube shows the researcher using customized SQL queries to manipulate the in flight entertainment system.
“After initial analysis we do not believe these systems can resist solid attacks from skilled malicious actors,” Santamarta wrote. “Airlines must be vigilant when it comes to their In-Flight Entertainment Systems, ensuring that these and other systems are properly segregated and each aircraft’s security posture is carefully analyzed case by case.”
“The ability to cross the ‘red line’ between the passenger entertainment and owned devices domain and the aircraft control domain relies heavily on the specific devices, software and configuration deployed on the target aircraft.” — Ruben Santamarta, IOActive
The researcher’s work discovered a number of unsettling facts. Firmware in flight entertainment systems was being posted online and on unsecured servers. That could allow anyone with the help of a few Google searches to locate the software, download it and analyze the firmware for exploitable holes.
Firmware from a single vendor is often modified to suit airplanes used by specific carriers. Santamarta said he found versions of the Panasonic firmware used on planes at 13 separate airlines online, including American, United, AirFrance, Virgin and KLM.
“Each airline or vendor that uses this is customizing it to their own needs,” he told Security Ledger in an interview. “In some deployments, an airline might have functionality that others don’t have.”
That makes it difficult to do uniform security assessments of a particular IFE software package, he said.
Santamarta did not have access to the entire code for the Panasonic Avionics IFE, only updates for parts of the overall IFE system, and so he was unable to perform a comprehensive audit. However, the application code he did analyze convinced him that IFE software used by many airlines is vulnerable to compromise.
“In-flight entertainment systems may be an attack vector. In some scenarios such an attack would be physically impossible due to the isolation of these systems, while in others an attack remains theoretically feasible due to the physical connectivity.”
Bridges between passenger domain systems like in flight entertainment and cockpit systems used to fly the plane are governed by electronic gateways that limit data (and thus, attacks) that flow from one to the other. But IOActive has demonstrated compromises of electronic gateway modules in non-airborne vehicles.
“The ability to cross the ‘red line’ between the passenger entertainment and owned devices domain and the aircraft control domain relies heavily on the specific devices, software and configuration deployed on the target aircraft,” Santamarta wrote.
A more likely scenario would be that hackers compromised systems used by crew to manage the cabin environment allowing attackers to “create a baffling and disconcerting situation for passengers,” he wrote.
IOActive research in 2013 identified vulnerabilities in satellite communications (SATCOM) software used on airplanes and ships, demonstrating that vulnerable SATCOM software could make it possible to compromise a system certified for use in the passenger cabin that interacts with devices certified for flight safety, such as those used in the cockpit, potentially putting the level A devices’ integrity at risk. (You can read the IOActive report here.)
The lack of consistency and governance creates the opportunity for mischief and even malicious attacks. Santamarta called for closer coordination between in flight entertainment software vendors, aircraft manufacturers and fleet operators. “Each plays an important role in assuring a secure environment,” he said.
Santamarta said that the current system of classifying different parts of the plane by their risk and applying different standards to the software that runs in each level doesn’t adequately account for the possibility of chained attacks that might jump from software running in one domain to more critical software running in another.
The question of whether attacks on in-flight entertainment systems could be used to enable attacks on avionics or other safety critical systems in flight is a hotly debated topic within the information security field. Over the years, there have been a number of efforts to probe this question – some better than others. In April, 2015, researcher Chris Roberts was taken into custody on a domestic flight by FBI agents in Syracuse, New York after tweeting about his ability to hack into in-cabin control and avionics systems from his seat. A subsequent FBI investigation alleged that Roberts was able to access avionics systems aboard a number of flights– a charge that Roberts denied.
That prompted a warning from the Government Accountability Office (GAO) about “significant security-control weaknesses remain that threaten the (FAA’s) ability to ensure the safe and uninterrupted operation of the national airspace system.”
Santamarta said that IOActive reported his findings to Panasonic Avionics in March 2015. However, the complexity of the IFE software deployment makes it difficult to know whether the issues have been fully resolved.
