Researchers from universities in Belgium and the UK have published research showing that a wide range of implantable medical devices, including implantable defibrillators are still vulnerable to wireless snooping and denial of service attacks.
The research, which mimicked the work of a naive (or “weak”) adversary, found that few security protections have been added to such devices, years after researchers first demonstrated that they are vulnerable to wireless attacks and other manipulation. The discoveries apply to at least 10 types of implantable cardiac defibrillators (ICDs) that are currently on the market, though the devices and manufacturers are not named.
The researchers, from Katholieke Universiteit te Leuven in Belgium (KU Leuven) and the University of Birmingham in the United Kingdom echoes the claims made by the firm MedSec earlier this year, which warned of security holes in ICD devices made by St. Jude in August. That research was the foundation of a call to short (or bet against) St. Jude’s stock by the firm Muddy Waters Research.
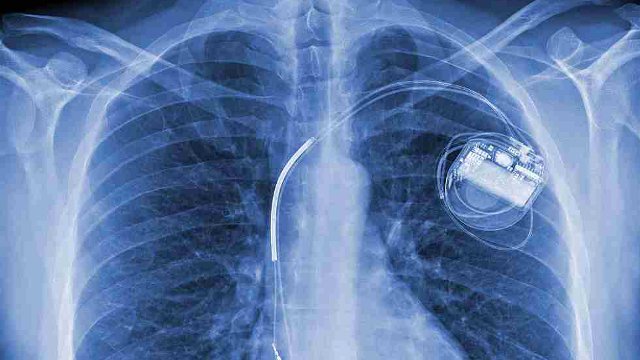
In the latest paper (PDF), the maker of the device and product are not named. However, researchers claim to have “fully” reverse-engineered the proprietary communication protocol that allows the ICD to communicate with the device programmer, a unit that doctors use to calibrate implantable defibrillators. The devices communicate over a long-range RF (radio frequency) channel and researchers discovered “several protocol and implementation weaknesses” that could be used to compromise the implantable devices.
[Read more Security Ledger coverage about the security of medical devices here. ]
Security weaknesses in ICDs that could be exploited by an attacker with physical proximity to the wearer are well documented. In 2012, the late Barnaby Jack, a security researcher at the firm IOActive, demonstrated how flaws in the connections between programmers and ICDs could be used to deliver a deadly, 830 volt shock from a laptop up to 50 feet away from a patient. Devices readily transmitted their serial and model number wirelessly, Jack discovered. That allowed him to reprogram the firmware of the device to administer the shock.
The notion of such attacks have also made it into pop culture – notably in an episode of the show Homeland. Former Vice President Dick Cheney was also said to have disabled remote connectivity for a pacemaker out of concern over malicious tampering with the device.
Despite those warnings, the researchers at KU Leuven and the University of Birmingham found little evidence that device makers had taken steps to secure the devices. The device studied by the researchers were vulnerable to snooping, with researchers able to decade and fully reconstruct the message format used to communicate.
Researchers also found that there was no mechanism for preventing so-called ‘replay’ attacks, in which captured traffic is sent back to a device, resulting in unwanted actions or behaviors from the device. Researchers found that messages sent between a programmer and a late model ICD were obfuscated, but that it was possible to snoop on wireless communications from the devices and identify patients by the device’s unique serial number. Adversaries could then “track, locate or identify patients” with the use of beacons designed to pick up on signals transmitted by the ICDs.” (A bit ‘Oceans 11,’ but certainly possible.)
Furthermore, data sent between the programmer and the ICD during a reprogramming session could allow adversaries to infer the patient’s treatment or the therapy details,” the researchers warned.
The research was performed without the presumption of prior knowledge of the ICD and relied on “inexpensive Commercial
Off-The-Shelf (COTS) equipment,” the researchers said.
“We demonstrate that reverse-engineering is feasible by a weak adversary who has limited resources and capabilities without physical access to the devices. Our analysis of the proprietary protocol results in the identification of several protocol and implementation weaknesses.”
