In-brief: the hacker known as Kapustkiy continued a string of attacks on diplomatic missions and related web sites last week, compromising Costa Rica’s embassy in China and the web site of a company offering services to travelers seeking visas to travel in Russia.
The serial data thief and gray hat hacker Kapustkiy continued his march to the sea last week, compromising the web site of a company that helps travelers in the U.S. obtain visas to visit Russia and Costa Rica’s embassy in China, The Security Ledger has learned.
The hacker, whose real identity is not known, posted information on more than 2,500 individuals seeking visas to visit Russia on Friday, just days after compromising the web site of Costa Rica’s embassy in China and leaking data taken from embassy servers.
Kapustkiy has made a name for himself in recent months as a talented and resourceful hacker of both commercial and government web sites – many of them linked to diplomatic missions. He has compromised computers operated by diplomatic missions and government agencies belonging India, Argentina and Hungry, among other countries. He’s decidedly nonplussed by that activity. Asked in an interview what was hardest about the hacks he had carried out, he responded “nothing.”
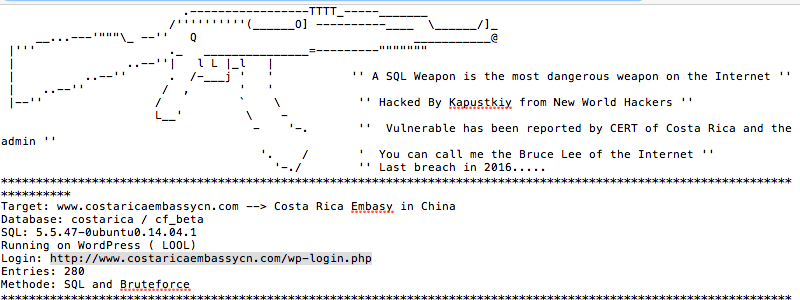
Most of his exploits have relied on technically simple and straight forward attacks on known vulnerabilities: weak user name and password combinations or SQL injection attacks. In the case of the Costa Rican embassy, the hacker told The Security Ledger that the site was vulnerable to SQL injection attacks, which use malicious commands in Structured Query Language to manipulate the back-end database applications that drive most modern web sites. But the administrators also relied on weak passwords to protect key accounts, the hacker told Security Ledger via Twitter.
The serial hacks highlight the lax state of security on many government and commercial web sites, despite years of warnings about the danger posed by weak and exposed web applications.
Kapustkiy, who describes himself as a 17-year-old hacker, claims that his hacks are designed to compel breached organizations to take security more seriously. His methods, including the theft and leaking of data, fall more on the “black hat” than the “gray hat” or “white hat” end of the security spectrum.
