
In-brief: a Distributed Denial of Service (DDoS) attack resulted in the loss of heating to two buildings in the city of Lappeenranta in eastern Finland according to a report by local media, the latest example of downstream effects of cyber attacks on connected infrastructure. Editor’s note: updated with comment from Mr. Rounela, the CEO of Valtia. 11/8/2016
A Distributed Denial of Service (DDoS) attack resulted in the loss of heating to two buildings in the city of Lappeenranta in eastern Finland according to a report by local media, the latest example of downstream effects of cyber attacks on connected infrastructure.
According to a published statement from the local IT management firm Valtia, and a report by the local Finnish Communications Regulatory Authority, the attack was noticed after a building automation system used in two properties began issuing strange alarms and could not be remotely accessed. The cause was a sustained denial of service attack that was flooding the building management system with bogus Internet traffic, causing it to restart every few minutes, and denying remote administrators at Valtia access to the device. The attack spanned from late October through November 3 to November 4, according to Simo Rounela, the CEO of Valtia. a report by the website Metropolitan.fi.
The result? “The majority of the controlled systems, such as heat distribution, ventilation and hot water went temporarily ‘broken’,” the company said in a statement. To fix it, a technician visited the buildings and removed the affected hardware from the Internet until the malicious traffic could be filtered out.
The attack is just the latest incident in which Internet-based denial of service attacks spill over into the physical world. In recent months, ransomware attacks on hospitals in the U.S., U.K. and on public utilities have resulted in disruptions of service. In October, a massive denial of service attack attributed to the Mirai botnet took the managed domain name system (DNS) provider Dyn offline, impacting high-profile customers including Twitter, Spotify, CNN and others.
A similar incident appears to have been behind the building automation attack, according to Rounela of Valtia, who wrote about the incident on the company’s web page. He cited a statement by Jarkko Saarimaki of the Finnish Communications Regulatory Authority attributing the attack to cyber criminals.
However, in a conversation with The Security Ledger, Rounela said that there is strong evidence that vulnerable and Internet exposed devices manufactured by the firm Fidelix, not an upstream attack on a DNS provider are to blame.
“There are about 1000 similar automation devices (on the) public Internet in Finland,” Rounela said in an email, citing a search using Shodan, the hardware search engine. “Some of the affected systems were not using Dynamic DNS services, so I can’t really say how the targets were chosen.”
He said that the building automation devices at two buildings that Valtia services were publicly addressable from the Internet and that is not uncommon in Finland. “It’s quite normal procedure to publish these automation stations to public Internet, because username and password protection should be enough – which it isn’t,” he wrote.
In a phone conversation, Rounela said that customers are often unwilling to pay for additional protection for the devices, such as a firewall. And, to date, attacks against them have been rare, making the case for more security even harder. ”
“Now we’re talking about two buildings, but the same systems are used in small hospital and daycare centers,” he noted. “This is the tip of the iceberg. We have two of these devices, but there are more than a thousand that are publicly addressable, so I’m quite sure we’re not the only company affected by this. “
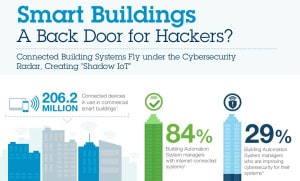
Building automation systems are known to be vulnerable to remote attacks and compromise. A recent survey of building automation system (BAS) operators found that only 29 percent had taken action or were in the process of taking action to improve cybersecurity for their Internet-connected systems. One if five of those professionals said they were not knowledgeable about cyber security and 58% said they were only “somewhat” knowledgeable about the topic. Also: nearly 4 in 10 said they did not know whether their building management assets might be connected to a public IP address, making them vulnerable to remote attacks.
[See also: IBM research calls out smart building risks.]
Researchers at IBM X-Force found that building automation systems suffer from a range of security issues, from weak authentication and authorization controls. Administrative web interfaces used to provide remote access to the systems also are vulnerable to application based attacks and lack basic security controls, said X-Force researcher Paul Ionescu.
Writing about the problem, Rounela of Valtia highlighted some of the problems. Building automation systems have revolutionized property management, allowing remote technicians to identify or even fix problems via a computer, rather than traveling to the site.
“Remote administration and monitoring of time spent using this can be significantly reduced. A single virtual inspection can be considered as dozens of real estate at the same time, as that would take place in one spot,” he wrote. However, companies such as his often rely on inexpensive IT assets that haven’t traditionally been subject to attack. That’s meant that customers “have not been able to ask or demand the right things, and equipment suppliers to sell” he wrote.
The possibility of cyber kinectic attacks in which the failure of systems resulting from Internet-based threats has impacts in the real world has caught the attention of regulators.
Source: DDoS attack halts heating in Finland amidst winter | Metropolitan.fi

