In-brief: Despite urging from lawmakers on Capitol Hill, the FCC is wary of changing rules to give ISPs a freer hand in cutting off access for infected Internet of Things devices, according to a report.
The recent attacks on managed domain name system (DNS) provider Dyn have ramped up attention within the beltway to securing the Internet of Things. Specifically: Senator Mark Warner (D-VA) last week wrote a letter to the Federal Communications Commission encouraging the FCC to block insecure devices like the cameras and digital video recorders that make up the Mirai botnet.
In his letter, Senator Warner raised concerns about whether the FCC’s Open Internet policy (PDF) tied the hands of Internet Service Providers when it came to shutting down compromised devices because of language prohibiting the connection of “non-harmful devices” to their networks. Warner is a member of the Senate Select Committee on Intelligence and a co-founder of the Senate Cybersecurity Caucus. Warner wondered whether more toothy language was needed to prevent a “tragedy of the commons” effect as insecure IoT devices become fodder for massive and crippling attacks.
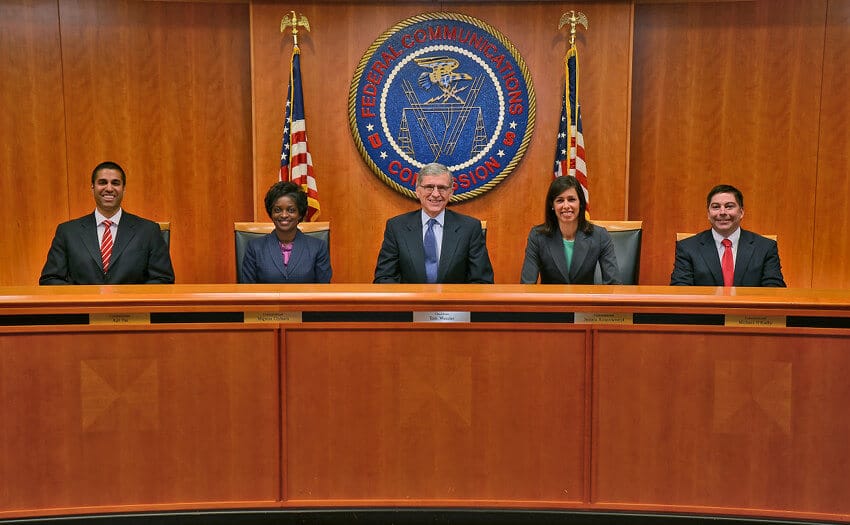
But according to this story over at Morning Consult, the FCC and its chairman, Tom Wheeler, seems disinclined to follow that suggestion. The prohibition on blocking ‘non harmful devices’ is not an issue, the FCC said. From the article:
That provision largely allows ISPs to determine for themselves whether devices are harmful. “The commission doesn’t intervene and lets providers go out and do what they can to address these practices,” the official said. “If someone goes too far, the FCC might say, ‘Hey, you’re violating the Open Internet rules.’”
The FCC could go further and use its Open Internet rules to bar ISPs from blocking any traffic emanating from IoT devices, or at least those with easily circumvented security protocols. But there is a fundamental hesitancy on the part of the commission to come down too firmly on network security. Part of that is due to ambiguity over the agency’s statutory authority on cybersecurity.
The FCC has mostly a “consultative role” when it comes to cyber security, explained Commissioner Ajit Pai in a press conference on Oct. 27. “There are other agencies that have a more well-defined space, legally speaking, and more well established expertise,” Pai said.
With no statutory provision directing the commission to create cybersecurity regulations, but the FCC retains “broad flexibility in determining whether security actions undertaken by telecommunication providers are reasonable,” the article notes.
A lack of clear ownership of cyber security within the Federal government is a concern. In just one example, cyber security guidelines have been issued – or promised – by a number of different agencies, from the Federal Trade Commission (FTC) to the Food and Drug Administration (FDA) to (most recently) the Department of Homeland Security (DHS).
The appointment of the first, federal Chief Information Security Officer (CISO) in September may help drive change. Greg Touhill, the CISO, will work from the Office of Management and Budget (OMB) to “drive policy and (the) implementation of leading cyber practices across federal agencies,” according to White House cyber czar Michael Daniel.
But that type of guidance and basic principles are “table stakes” for making a secure and viable Internet of Things, said Joshua Corman, the director of the Cyber Statecraft Initiative at the Atlantic Council’s Brent Scowcroft Center in a call with reporters last week. Both voluntary, industry led guidelines and government imposed mandatory standards may be warranted, Corman said. But there is “no silver bullet to fix this.” The solution may be to embrace ideas that have been proposed in the past: from safe handling labels, akin to what adorn food and other products to more toothy software product liability laws that push responsibility down to software publishers for security and privacy. “We have a large list of good reasons to resist looking at things like minimum hygiene standards or software liability. But, on the other side of the scale, there’s a long and growing list of arguments to have a look at these things,” Corman said.
Source: FCC Holds Off on Security Mandates for Internet of Things – Morning Consult
