
In-brief:Cyber criminal groups are racing to gain control over a population of insecure “Internet of Things” devices, with new malware families targeting embedded devices appearing at a steady rate and a noticeable uptick in so-called “brute force” password guessing attacks against embedded systems.
Cyber criminal groups are racing to gain control over a population of insecure “Internet of Things” devices, with new malware families targeting embedded devices appearing at a steady rate and a noticeable uptick in so-called “brute force” password guessing attacks against embedded systems.
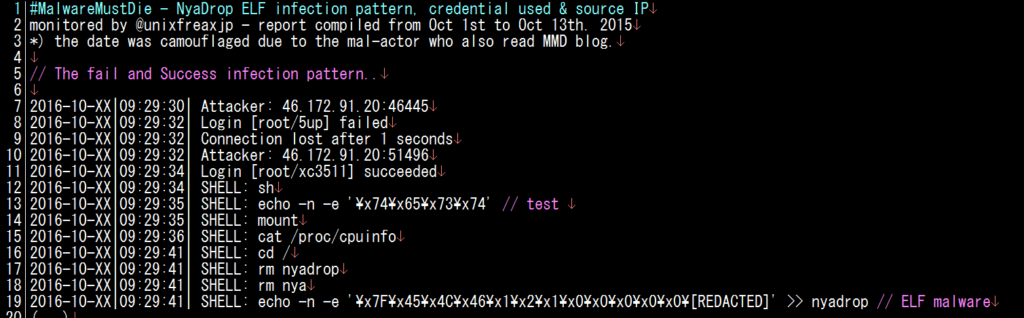
The latest, NyaDrop, was the subject of an analysis on the web site Malware Must Die on Thursday. As with other, similar threats, including the Mirai malware, it is spreading by locating and attempting to log in to embedded systems using known, default user name and password combinations.
Specifically, NyaDrop looks for embedded systems that use the MIPS architecture, a common feature of broadband routers and other small, embedded systems. Login information captured by the researchers at Malware Must Die suggest that the attacks are looking for common hardware like DAHUA brand IP-enabled network security cameras, though the attackers are likely targeting a range of Internet connected devices.
As Security Ledger reported, a vulnerability in the Linux operating system used on many DAHUA devices makes them easy targets for attack. Simply entering a user name with too many characters can cause an overflow error that gives the attacker access to the camera’s administrative web interface.
[Read more Security Ledger coverage of the Mirai botnet.]
Mirai isn’t the only malware targeting embedded devices like cameras, broadband routers and home-based “network attached storage” (or NAS) devices. Akamai Technologies published research last week on a similar botnet, dubbed SSHowDown, that used a well known configuration error in Secure Shell (or SSH) to commandeer Internet of Things device as proxies to route malicious traffic to their desired target.
A variety of Internet-connected devices have been observed taking part in web-based “credential stuffing” campaigns, a kind of slow motion brute force attack in which attackers leverage stolen (or leaked) user name and password combinations to try to hack into accounts on a revolving list of popular sites. The devices taking part in the attacks including IP enabled cameras, network video recorders, network attached storage (NAS) devices and even satellite antennas, according to Ory Segal, the Senior Director of Threat Research at Akamai.
Johannes Ullrich at the SANS Internet Storm Center also posted a blog last week about the brief life of Internet connected DVR (digital video recorders), noting that a test device he made publicly accessible was attacked about once every minute using variations of the brute force attack that Mirai, NyaDrop and other “thing” malware uses to spread.
The existence of vulnerable embedded systems isn’t new. In fact SANS ISC was warning about exposed DVR and NAS devices two years ago.
What seems clear, however, is that there is a land rush going on for insecure and weakly secured Internet of things devices. In his blog post, for example, Ullrich noted that SANS ISC has recorded a marked increase in login attempts using the default password “xc3511” which is used across a wide range of white labeled connected devices including cameras and DVRs.
At Malware Must Die, researchers note that NyaDrop first appeared in May in a loosely organized and ineffective attack. But the malware returned in September with improvements amid a “race to infect the known IoT vulnerable sector.” In fact, the NyaDrop malware bears close resemblance to malware attacking Ullrich’s exposed DVR a week earlier, though it appears the two families are different.
With improvements to the security of the Windows operating system, embedded devices, many running versions of Linux, have become the new low-hanging fruit for cyber criminals and others who wish to command legions of Internet connected devices. In the case of Mirai, a global botnet of hundreds of thousands of commandeered cameras, DVRs and other devices was used to generate the largest denial of service attacks yet measured, with more than 600 Gigabits per second of junk traffic taking down websites like the security blog Krebs on Security and the French hosting firm OVH.
Weak supply chain controls are a major contributor to the problem of weak and insecure embedded systems. In the case of Mirai, a common, China-based supplier of management software, XiongMai Technologies, was abused by cyber criminals to install the Mirai software on hundreds of thousands of DVR, NVR (network video recorder) and IP cameras globally, according to an analysis by the firm Flashpoint.
