In-brief: cellular gateways made by Sierra Wireless may be susceptible to the Mirai malware, the Department of Homeland Security warned on Wednesday.
The Mirai malware that is behind massive denial of service attacks involving hundreds of thousands of “Internet of Things” devices may also affect cellular modems that connect industrial equipment and other critical infrastructure to the Internet.
That, according to an alert issued by the Department of Homeland Security (DHS)’s Industrial Control System CERT on Wednesday warning that cellular gateways manufactured by Sierra Wireless are vulnerable to compromise by the Mirai malware. While the routers are not actively being targeted by the malware, “unchanged default factory credentials, which are publicly available, could allow the devices to be compromised,” ICS-CERT warned.

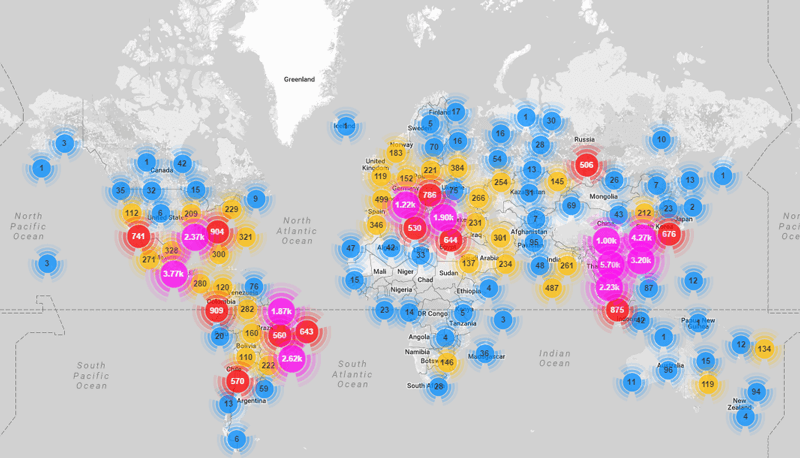
The alert comes after a number of reports identified devices infected with the Mirai malware as the source of massive denial of service attacks against media websites like Krebs on Security and the French hosting company OVH. The attacks emanated from a global network of hundreds of thousands of infected IP-enabled closed circuit video cameras, digital video recorders (DVRs), network video recorders (NVRs) and other devices.
Analysis by the firm Imperva found that Mirai is purpose-built to infect Internet of Things devices and enlist them in distributed denial of service (DDoS) attacks. The malware searches broadly for insecure or weakly secured IoT devices that can be remotely accessed and broken into with easily guessed (factory default) usernames and passwords.
[Read more Security Ledger coverage of the Mirai malware.]
Once located, these devices are subjected to brute force attacks – basically automated password guessing using a pre-programmed list of user name and password combinations such as “admin/admin,” “support/support,” “root/admin” and so on.
That kind of activity apparently caught the eye of technical staff at Sierra, who warned that its own devices contain default credentials that could make them vulnerable to compromise if the credentials had not been changed subsequent to installation and deployment.
Sierra said in an alert that the company has “confirmed reports of the ‘Mirai’ malware infecting AirLink gateways that are using the default ACEmanager password and are reachable from the public internet.” Sierra Wireless LS300, GX400, GX/ES440, GX/ES450, and RV50 routers were identified in the bulletin as vulnerable to compromise by Mirai.
Infected devices may become inoperable or suffer from performance degradation given that demands of scanning their local network for other devices to infect. Furthermore, devices attached to the gateway’s local area network may also be vulnerable to infection by the Mirai malware, ICS-CERT warned.
Sierra Wireless asked affected users to reboot their gateway. Mirai is memory resident malware, meaning that is erased upon reboot. Furthermore, administrators were advised to change the password to the management interface by logging in locally, or remotely to a vulnerable device.
Sierra markets AirLink gateways as a workhorse for IoT deployments in a variety of “mission critical” contexts from energy to smart city. That makes the threat of Mirai infections potentially dire, as a gateway engaged in a denial of service attack may be unable to provide connectivity for downstream IoT devices, resulting in a loss of service or even cyber physical events.
While many deployed cellular gateways are protected from roving Internet scans, tens of thousands of devices are publicly accessible. A scan for Sierra GX400 gateways using the Shodan search engine, for example, turned up more than 6,000 such devices that are reachable from the public Internet.

Whelp, exposing insecure devices with default or easily guessed passwords to save a few bucks and the whole internet suffers. There’s nothing we can do, as long as profit is a motivator. I don’t know how bad Sierra is or has been with security in general, but the companies making DVRs, refrigerators, light bulbs and the like all exposed to the internet with weak security and no firmware updates in sight are the problem here.
How about an expensive tax or fine for companies that don’t deploy basic security measures for these things? Too bad it’d be impossible to enforce…