In-brief: A sustained denial of service attack against Dyn, a provider of hosted domain name system (DNS) services hobbled some of the Internet’s most trafficked websites on Friday. Its source or intended purpose still aren’t known.
A sustained denial of service attack against Dyn, a provider of hosted domain name system (DNS) services hobbled some of the Internet’s most trafficked websites on Friday including micro blogging site Twitter, the music streaming service Spotify and the website of cable news giant CNN.
DYN, headquartered in Manchester, New Hampshire in the U.S. acknowledged an “ongoing service interruption of our Managed DNS network” at around 12:30 PM UTC, 8:30 AM local time. That announcement followed widespread complaints of service outages by users of services like Twitter and Spotify in Europe and North America early Friday.
While DNS service was nominally restored at just past 1:30 PM UTC (9:30 AM local time on the East Coast in the U.S.) DYN appears to have struggled all Friday to fend off attacks. Notices posted on the company’s Status Page at 3:52 PM UTC (11:52 AM local time) said the firm “have begun monitoring and mitigating a DDoS attack against our DYN Managed DNS infrastructure.” A message posted at 7:43 UTC, 3:43PM local time reported that “our engineers are continuing to investigate and mitigate several attacks aimed against the DYN Managed DNS infrastructure.”
Efforts by Security Ledger to contact DYN for comment by both email and phone were not returned.
The Domain Name System (or DNS) translates human-readable Internet domains, such as “twitter.com” into the numeric Internet Protocol (IP) addresses used by Internet-connected machines to communicate. DNS is one of the pillars of the modern Internet, helping users easily find the site they are trying to reach. But it also uniquely vulnerable to attack, according to experts at Arbor networks.
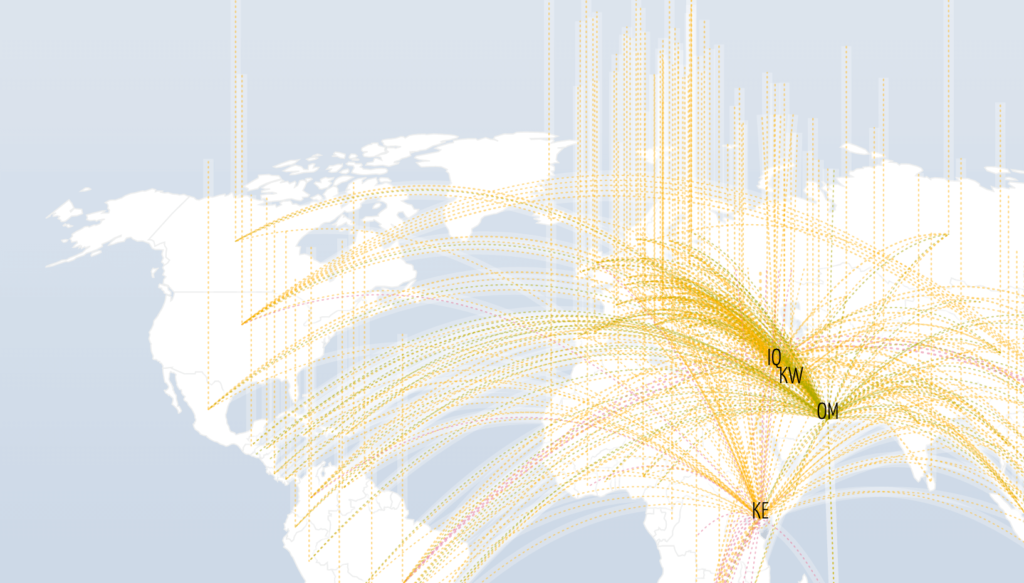
To scale globally, DNS has evolved into a complex network made up of “root servers” controlling top-level domains such as .com, .gov, and .org, Global Top Level Domains (TLDs) controlling regional domains such as those for France (.fr) or the United Kingdom (.uk), authoritative servers controlling specific domains such as myfavoritestore.com and a huge number of so-called “recursive resolvers” that end-user systems connect to. A request for a web domain (say securityledger.com) sent from a user’s machine would be sent to a recursive resolver and that resolver would work with the root, GTLD and varying levels of authoritative servers to track down the DNS authoritative server responsible for the domain from which it would receive a DNS reply.
The tightly interconnected DNS network makes it vulnerable to denial of service attacks at any point in the chain of trust, Arbor notes. DDoS attacks against recursive DNS servers may shut down DNS resolution regionally for a specific ISP or cable modem provider. In that instance, none of the ISPs users would be able to resolve domain names at all. Alternatively, DDoS attacks against authoritative domain servers may shut down DNS resolution for a specific web domain or a group of domains. The attack on DYN falls into that category. At the next level up, a DDoS attacks against a root or GTLD system could impact all domains for a country or even an entire class of domains – such as all .COM sites.
It was unclear early Friday what was the source of the denial of service attacks against DYN’s DNS infrastructure. Recent weeks have witnessed the largest denial of service attacks on record launched from a network of Internet connected devices infected with a variety of malicious software programs including one called “Mirai.” Many of those are non-traditional endpoints such as cameras, digital video recorders and network attached storage (NAS) devices.
But a massive denial of service attack may not be necessary to knock DYN’s DNS service offline, said Andy Ellis, the Chief Security Officer at Akamai, a content distribution network that also offers DNS services.
Ellis said that most companies that offer DNS services to their customers strive for a “heterogeneous” infrastructure modeled on that used to keep the DNS root servers online. That includes high density deployments of name servers in high availability data centers with load balancing technology to keep any server from being overloaded and an a distributed, global network of individual servers that might serve specific customers (say an ISP) or a geographic area. Attacks against any one server or location can then be spread across the entire network, preventing a failure, Ellis said. “That’s the right way to do it,” Ellis said.
Equally mysterious is the purpose or target of the attack, Ellis said. It is well-known within the DDoS for hire community that managed DNS services like DYN’s are a rich target, as taking one out will have widespread collateral damage. “People do know that if you hit a major player and impact them it will have a widespread, collateral effect,” he said.
