In-brief: A researcher from the firm Trustwave warns that Trane ComfortLink smart thermostats suffer from a string of security woes, including hard coded administrator credentials.
Smart, remotely controlled home thermostats have been the poster children of the Internet of Things ever since the start-up Nest (now Google) kicked off the smart home trend with its dazzling rethink of an old and ignored product. But the products aren’t without their risks.
Researchers at the firm Trustwave are reporting that smart home thermostats manufactured by the firm Trane are vulnerable to a remote, Internet-based attack that could allow an attacker to control the heating or cooling in a home or observe a family’s waking and working schedule. That, according to a blog post Monday by Trustwave researcher Jeff Kitson.
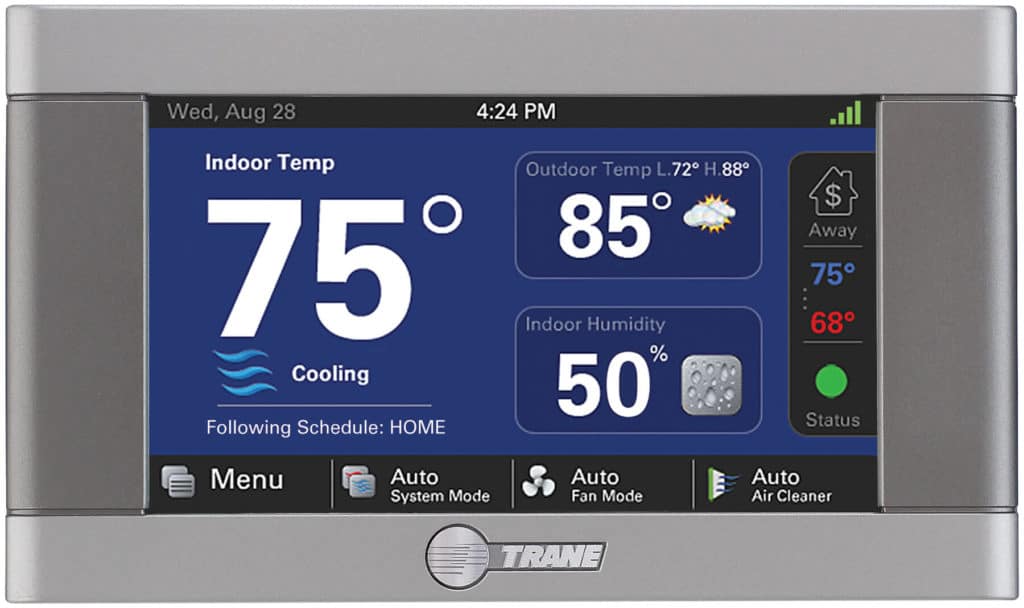
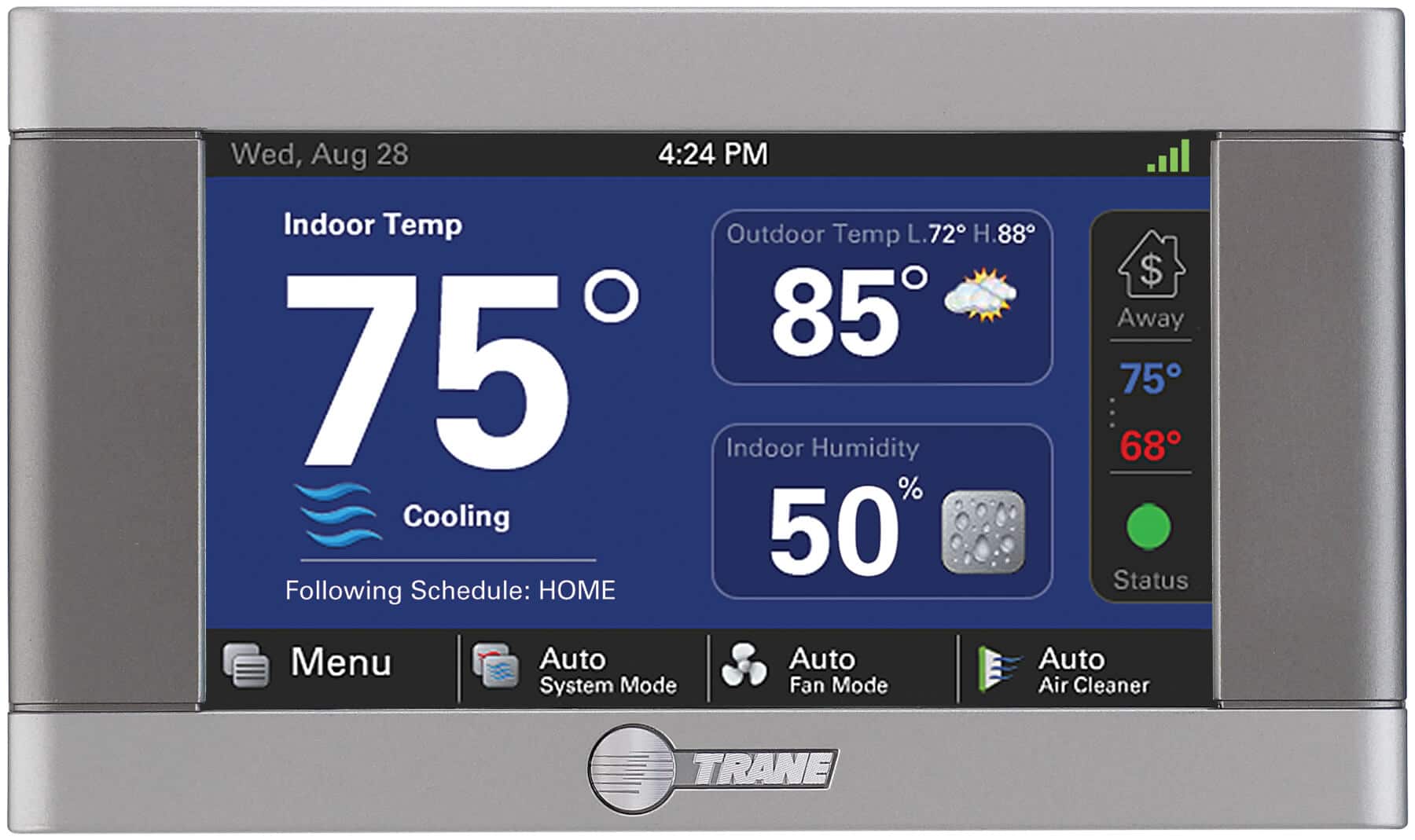
Kitson said that he began investigating the Trane ComfortLink XL850 thermostats after one was installed in his home. The device boasts WiFi connectivity, remote service, remote control and ZWave features. A partnership with the firm Nexia allows thermostat owners to monitor and manage their thermostat via a website or a mobile application.
“When you combine hardcoded credentials with a network accessible port, you have a device ripe for attack from the network or even …the Internet.” — Jeff Kiton, Trustwave.
But Kitson said his investigation into the Trane and Nexia technology revealed a host of now-common problems. Specifically, Trane ComfortLink thermostats running firmware version 3.1 or lower were found to have “hardcoded credentials” – basically: administrative user names and passwords that are written into the device’s software and can’t be changed.
Additionally, Kitson warned that the ComfortLink devices use a custom protocol and a predictable port number to administer remote access to the device. Combined with a known, hardcoded administrative account, that spells trouble, he said.
“When you combine hardcoded credentials with a network accessible port, you have a device ripe for attack from the network or even an attack from the Internet if the thermostat is exposed through the router,” Kitson wrote. Only a few dozen ComfortLink devices are, based on Kitson’s research – most of them in the United States.
Trustwave contacted Trane regarding the vulnerabilities and, after some false starts, said the firm was able to address the security issues and issues an update to any deployed devices starting in July.
Additionally, Trustwave informed Nexia, a partner company of Trane and the mobile app used to control the XL850, that Github repositories they maintained containing raw source code for controlling backend command and control services for these thermostats were publicly accessible. “A number of configuration files, encryption salts and secret keys were present in the repositories increasing the risk to customers,” Trustwave said.
Working through Trane, steps were taken to clean up the publicly exposed confidential code from Nexia.
Security problems with smart home products are well documented. In March, the firm BitDefender published a case study on four common IoT platforms. The company found that authentication features for such devices are inadequate, among other problems.
In April, Federal data protection authorities from 29 countries including the U.S. and Canada have turned their collective attention to the Internet of Things in an annual “privacy sweep” of connected devices including personal health products. The Global Privacy Enforcement Network, (GPEN) said that the “explosion of Internet-connected everyday objects and privacy concerns surrounding our increasingly wired world” were what prompted the group to urge countries to focus on the Internet of Things during the 2016 global privacy Sweep.

Well I guess I don’t have to spend the weekend fiigrung this one out!
The days are long, but the years are short. I don’t want to miss them! For more short and sweet ideas on how to stop and smell the roses, to enjoy the little things in life, check out my 31 Days to Smell the Roses series.
Thanks for the update where Satan and all the other enemies of mankind are going to congregate over the next month. I will be sure to be no where around. Whose death will they shout out for THIS time?
This issue has a stunning photo of Edward Fox by Cecil Beaton, as well as a fantastic interview with him in connection with THE DAY OF THE JACKAL. I know you can't post everything, but I'm surprised that you didn't choose this one.