
In-brief: Security improvements for connected cars may be years away, as both the government and industry struggle to catch up on the cyber security issue, a GAO report found.
Software based attacks on connected vehicles are a real problem, but help – in the form of more secure vehicles from Detroit or new regulations and standards from Washington D.C. – are likely years from being realized, according to a report from the Government Accountability Office (GAO).
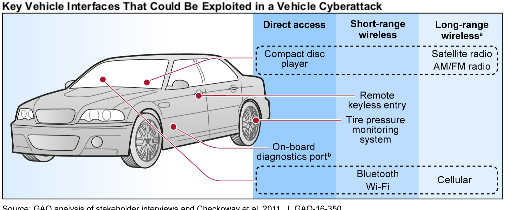
The GAO issued a report last month (PDF) paints a worrying picture as regards vehicle cyber security. GAO tells Congress that modern vehicles feature many communications interfaces that are vulnerable to attack, and noting that remote, software based attacks that affect critical vehicle functions have already been demonstrated by researchers. Unfortunately, measures to address those threats are likely years away, as automakers work to design more secure in-vehicle systems and regulators, like that National Highway Traffic Safety Administration (NHTSA) struggle to determine their role and the scope of possible regulations.
In either case, help is likely years away, the GAO concluded, citing information gleaned from automotive industry “stakeholders.”
The GAO report, addressed to “Congressional Requestors” was a response to a request to review cybersecurity issues that could impact passenger safety in modern vehicles. The report surveyed automakers, suppliers and other industry representatives, as well as representatives of relative governing bodies about issues such as cybersecurity vulnerabilities in modern vehicles that could impact passenger safety, technologies that could mitigate vulnerabilities and threats, the views of stakeholders on automotive cyber security and Department of Transportation efforts to address vehicle cybersecurity.
Despite independent research dating back more than five years showing that remote, software based attacks on vehicles were technically possible, GAO notes that both the government and industry have been slow to respond.
“Despite awareness of risks related to vehicle cybersecurity since at least 2011, the auto industry and NHTSA have only recently sharpened their focus on this issue,” GAO said.
NHTSA, the government’s lead body on vehicle safety, has taken “several important steps” on vehicle cybersecurity since 2012, GAO noted that the agency has established a vehicle-cybersecurity research program and is “soliciting industry input on the need for government and voluntary industry
standards.” (Security Ledger reported last week on NHTSA’s solicitation for help drafting cyber security standards.) However, “NHTSA does not anticipate making a final determination on the need for government standards until 2018 when additional cybersecurity research is expected to be completed,” GAO noted.
So too on industry efforts to address vehicle cybersecurity. The development of an Automotive ISAC and a voluntary design and engineering process standard for cybersecurity—are still in their early stages, GAO notes.
“As such, some of these government and industry efforts to address vehicle cybersecurity are unlikely to provide many benefits for vehicles already operating on the roads today or those currently in the design and production stages,” the report notes.
[Read Security Ledger’s coverage of connected vehicles here.]
The gulf between offense and defense is a problem. “Given that NHTSA and industry stakeholders expect the threat of a vehicle cyber attack to increase in the coming years as autonomous and connected-vehicle technologies are deployed, it will be important for NHTSA to continue to take proactive steps in the interim to ensure that it is meeting the agency’s goal of being ahead of vehicle cybersecurity
challenges,” the report concluded.
The recall of 1.4 million Fiat Chrysler vehicles following reports of a remotely exploitable security hole sets a useful precedent going forward, GAO concluded. “The agency’s planned guidance outlining when cybersecurity vulnerabilities constitute safety defects should help ensure consistent responses when cybersecurity vulnerabilities are identified,” GAO said. However, “until NHTSA defines and documents the agency’s role and responsibilities in the event of a real-world vehicle cyber attack affecting safety-critical systems, it may not be in a position to quickly and effectively respond should a threat materialize.”
Lawmakers have become increasingly concerned about the security of connected cars, as automakers move forward aggressively with new software based features including hands free driving, over the air software updates and in-vehicle wi-fi hot spots.
In a September 16 letter to leading automakers, Senators Edward Markey and Richard Blumenthal requested more information on security protections in late-model vehicles, citing recent demonstrations of wireless hacks, including an attack on Fiat Chrysler Jeep Cherokee, which was featured at the Black Hat Briefings in August.
The letter asked leading U.S. based and foreign automakers for updated information about protections “against the threat of cyber-attacks or unwarranted invasions of privacy related to the integration of electronic systems into and within automobiles.”
The letter was addressed to the chief executives of the largest car makers in the world, including US auto companies Ford Motor Co., General Motors, Tesla and Fiat Chrysler, as well as the North American subsidiaries of leading European, Korean and Japanese firms like Mercedes-Benz, Porsche, Volkswagen, Subaru, Honda and Toyota.
The letter follows a similar inquiry in 2013, and the release of a report on security and privacy gaps in vehicles released in February 2015 and then proposed legislation by the two senators in late July. The Security and Privacy in Your Car (SPY Car) Act would direct the National Highway Traffic Safety Administration (NHTSA) and the Federal Trade Commission (FTC) to establish federal standards to secure cars and protect drivers’ privacy.

