In-brief: The discovery of a malicious link buried in software for a common IP camera sold on Amazon and other online retail outlets is just the latest example of supply chain based threats to connected products.
A sweet deal for Internet-enabled cameras on Amazon.com proved to be a bitter pill for security researcher Mike Olsen recently, after the discovery of a link to a malicious web site buried in the web-based management interface for the cameras.
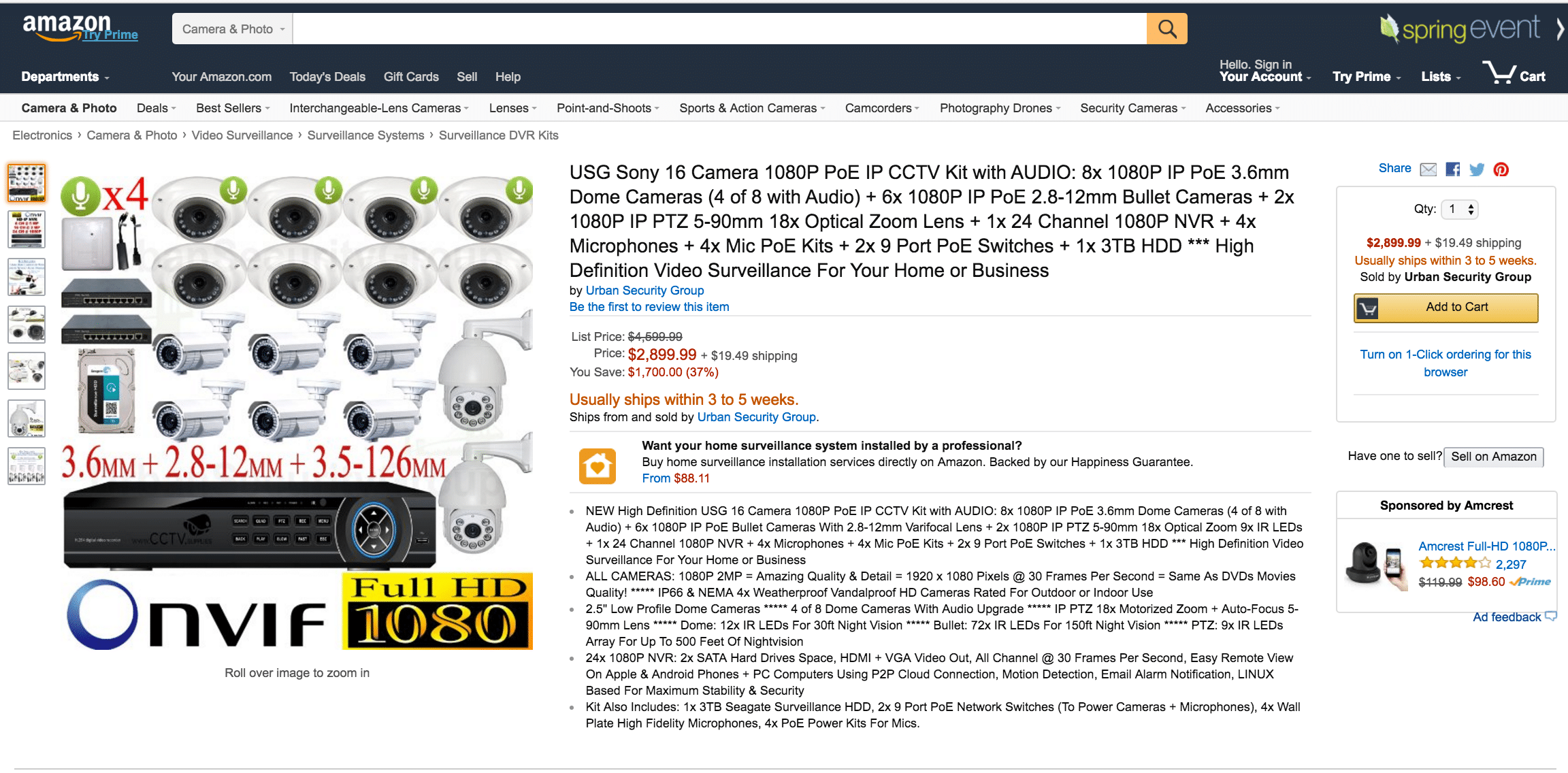
In a blog post on April 9 Olsen wrote about purchasing a Sony 16 Camera 1080P Power over Ethernet IP-based closed circuit camera (CCTV) from an online vendor using the name Urban Security Group. The product page has since been taken down by Amazon.
When trying to configure the set-up Olsen noticed that the web management interface for the product was amiss: displaying the video stream from the cameras but not any administrative settings.
After digging into the code for the management page, Olsen found an iframe “tucked at the bottom of the body tag … linking to a very strange-looking host name.”
The web site in question was Brenz[.]pl, a website known for distributing fake antivirus software back in 2009 and resurfacing in 2011, according to a report from security company Sucuri.
While the Amazon product page for the camera in question has been removed, Urban Security Group continues to offer CCTV products on Amazon.
This is not the first time the IP cameras have been found harboring malicious code. Olsen notes a thread in an Australian support forum for weatherproof IP surveillance cameras in February in which users complain about a tampered firmware that points to the same, Polish domain as Owens’ camera.
For now, the domain in question has been seized and sinkholed by the Polish CERT (Computer Emergency Response Team), so clients redirected to it can no longer get infected. In the past, the domain has been linked to fake antivirus software campaigns.
The issue is just the latest to highlight vulnerabilities in the global software supply chain. In March, Rotem Kerner, a security researcher at the firm RSA, disclosed a serious vulnerability in firmware made by the China-based company TVT and used by over 70 different CCTV vendors.
In January, AMX, a division of the firm Harman Ltd. acknowledged that it shipped software for secure conferencing equipment used by the U.S. government and military with an undocumented “backdoor” account. That fix came almost one year after the firm was notified of the existence of the back door account by SEC Consult, an independent security research organization.
Surreptitious changes to firmware used by connected devices is a convenient way for cyber criminals to establish a foothold on legitimate web domains. Online resellers, not to mention businesses and consumers typically monitor the devices for malicious activity, nor is it common to check that the products run the exact software intended by the manufacturer.
Researchers at Vectra security company demonstrated this type of attack by turning a D-Link web camera into a backdoor that allowed them access to the network without raising suspicions.
In the most recent incident, the source of the compromise is not clear. The retailer did have access to the product during the packaging procedure. Mike Olsen said that “the boxes didn’t have any security stickers.”
In a report in February, researchers from IEEE warned about the risks posed by new, connected devices including wearable technology. Such devices typically support diverse ecosystems, but may not have security mechanisms to allow different parts of those ecosystem to verify their identity and integrity.
Without proper security controls, compromises from spoofed devices, “man in the middle” attacks or malicious firmware updates, the report says.

