In-brief: The same wireless software that powers a consumer quadcopter is also under the hood of Tesla’s Model S, according to a leading security expert – underscoring the increasingly long and complex software supply chain for connected products.
One of the big challenges facing companies and individuals that wish to secure the Internet of Things is the sheer complexity of connected devices – and the interconnections between them.
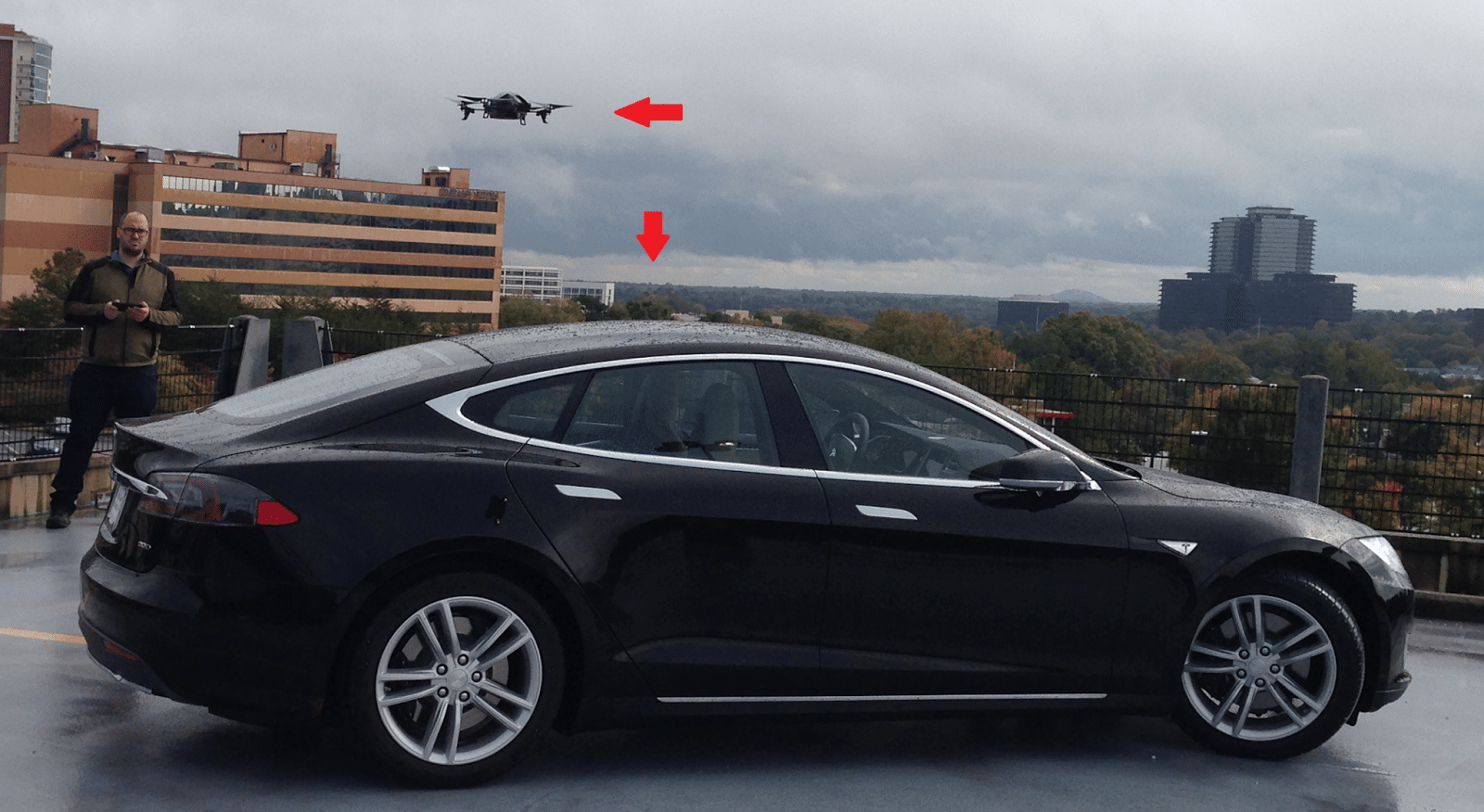
Exhibit #1: Tesla Motors sleek Model S electric sedans, which retail for over $60,000 and the AR Drone from the french firm Parrot SA – a consumer quadcopter that starts at a reasonable $405 on Amazon.com. What do the two products have in common? Lots, according to security expert Rob Graham of the firm Errata Security.
Writing on his blog earlier this week, Graham noted that the Tesla and the AR Drone appear nearly identical to a wireless sniffer when connected to the same wireless network, with similar MAC (media access control) addresses beginning with the code “90:03:B7” for Parrot SA. A coincidence? Hardly: Tesla’s sedans appear to use Parrot’s wireless access software to manage connections to wireless hubs at its servicing centers, where cars upload data to a Tesla Service access point upon arrival, Graham wrote. That’s the same software that allows Parrot’s AR Drone to serve as an access point for mobile phones, like the iPhone, to connect to and navigate the device.

Why use a consumer drone maker’s software on a $60,000, ultra-sophisticated electric car? Because it works, Graham says. Besides, Parrot – a 20-year-old company with 850 employees that is based in Paris – started off serving the automotive industry. Drones were merely an opportunistic play into a hot market in 2010 along with “connected” photo frames and wireless speakers.
The company Parrot SA started out creating kits for cars that contain WiFi, Bluetooth, and voice control. Since they were already building embedded WiFi, they apparently used that expertise to make a flying drone controlled via WiFi (from an iPhone app). So while it seems odd that Parrot would sell both drones and automobile components, it’s actually overlapping expertise.
In fact, its likely that the same software is already embedded in a number of other vehicles and “connected devices” that need similar wireless connectivity. Automakers like Tesla – sophisticated engineering firms – are loath to reinvent the wheel. Even revolutionary vehicles like the Tesla are just agglomerations of hardware and software created by other, third-party firms with a long list of customers.
“Car companies can’t innovate everywhere,” Graham said in an interview with The Security Ledger. “They have to rely on their supply chain partners to innovate for them.” Even high-profile features, like the recent Tesla “autopilot” may have been developed by engineers and developers working for Tesla partners, Graham said.
The problem, for automakers, is that long and complex software supply chains may introduce what are sometimes referred to as “common mode” vulnerabilities into vehicles and other life-sustaining equipment.
“‘Supply chain’ risks are the next battle ground,” Graham wrote in an e-mail. “We see this already with how rental car agencies put off safety recalls.” As yet undiscovered security holes in third-party vendors like Parrot could pose safety and privacy risks to consumers through a wide range of products – from $400 drones to $60,000 cars. That’s especially true if the vendor who manages the customer relationship chooses not to pass security fixes through to their customers, or rewrite code to take responsibility for risks, Graham said.
