Known versions of ransomware can run on smart TVs that use Android and other mobile and embedded device operating systems, according to research by Symantec.
Owners of smart TVs that use Alphabet’s Android operating system are susceptible to becoming victims of ransomware and could be even more difficult to disinfect than PCs, according to a researcher with the security firm Symantec.
The experiment, on a smart TV running a custom version of the Android mobile operating system, could be adapted for use against other “smart” and connected devices running othe popular smart television operating systems like Tizen, Web OS and Firefox OS, according to a report by Candid Wueest and published on Symantec’s research blog.

Android is a popular choice for smart TVs, with major vendors such as Sony choosing Android as their go-to OS for smart TVs. Previous research from security experts has shown that mobile phones as well as smart watches are vulnerable to malicious attack, including so-called “ransomware,” which encrypts sensitive files on the victim’s computer and then promises to provide a key to decrypt the files in exchange for a payment.
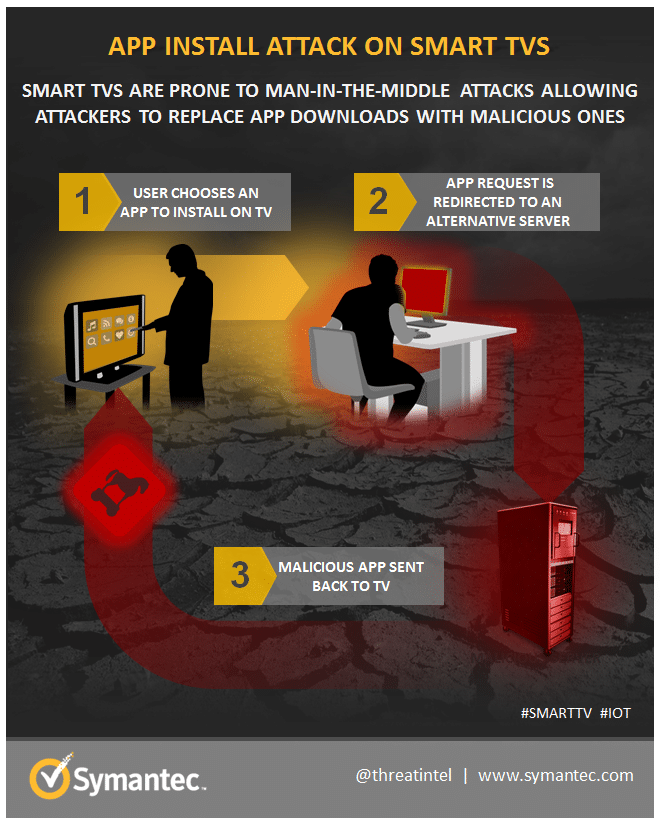
Wueest of Symantec found that a flaw in a gaming portal on the device allowed users to install applications by sending unencrypted requests to the server. Using a variant of the classic “man-in-the-middle” attack, Wueest intercepted a request and modified it to point to a server with a malicious version of the requested package. Unless other security measures are in place, such as signing the package, the user ends up downloading and installing the malicious payload instead of the legitimate application.
To demonstrate the danger to smart TV owners, Wueest hijacked the installation of a game app and replaced it with a version that looked just like the legitimate one. This one was repackaged with the malicious component, which deployed when the game launched.
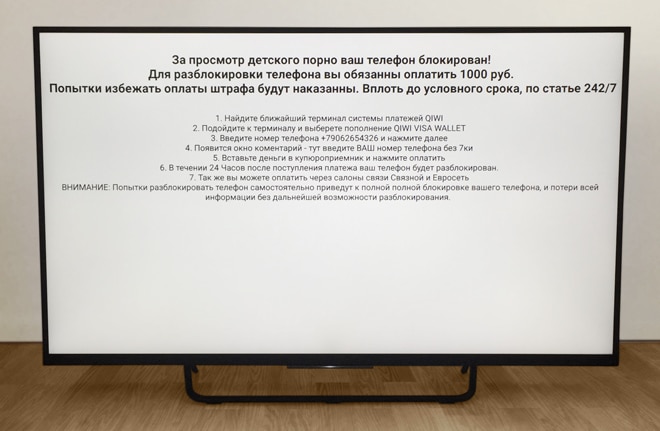
In most cases, ransomware locks Android phones by covering the screen with a persistent message. It cannot be easily removed and survives reboot, demanding money in exchange for setting free the device.
“As expected, the threat worked and locked the TV after a few seconds, displayed the dreaded ransom note on the screen, and made the TV unusable. This particular ransomware displays the ransom note every few seconds which prevented me from carrying out any meaningful interaction with it,” Wueest wrote on Symantec’s blog.
Default Android security settings only allow downloads only from legitimate domains, limiting opportunities for attackers to push malicious applications onto smart devices running the Android OS. However, Wueest said that many TV makers allow firmware updates from web sites that do not use SSL, making man in the middle attacks an issue. Also: other mobile operating systems do not have such precautions enabled by default.
Disinfecting the device proved difficult. He managed to clean the device because a USB debugging feature had been enabled, allowing an Android Debug Bridge (ADB) connection to the device, which gave him direct, command line access to the device’s operating system. Only a tiny minority of smart television owners would have the sophistication to disinfect the TV themselves, Wueest speculated.
Ransomware is a growing problem for users of personal computers. The FBI issued a notice in June, saying that it had received 992 complaints related to just one variant of ransomware, CryptoWall, between April 2014 and June 2015. Losses from those scams totaled $18 million. Speaking in October, the head of the Boston office of the FBI warned that law enforcement is often not able to break the encryption used by the malicious programs, leaving affected firms to either go without their ransomed data, or to pay the ransom to get it back.
Experts say that the growth of the Internet of Things could, potentially, create new opportunities for ransomware scammers. Forrester Research warned that medical devices and other wearable technology could also be leveraged for financial extortion.
Users can reduce the ransomware risk by taking the time to check the security settings of the device and restricting installation of applications to verified locations only.
Paramount for keeping IoT devices in the local network safe is securing access to the home router by changing the default password and enforcing strong encryption for the Wi-Fi network.

Pingback: Errata: In-game Nuke Disarmament,VR, Toy Hack, Smart TV hack, Trump & Heller | Neurovagrant
Pingback: Samsung Positions TV as Secure IoT Hub For Home | The Security Ledger