In-brief: Trend Micro published research on vulnerabilities in a technology dubbed SmartGate wireless technology that could expose private information on vehicle owners and passengers, or leave the wireless network vulnerable to takeover by a malicious actor.
The parade of worrying news about the security failures of connected vehicles continues this week, after last week’s disclosure of a major vulnerability in a range of vehicles by Fiat Chrysler that make it possible to launch wireless attacks that can affect steering, acceleration and braking.
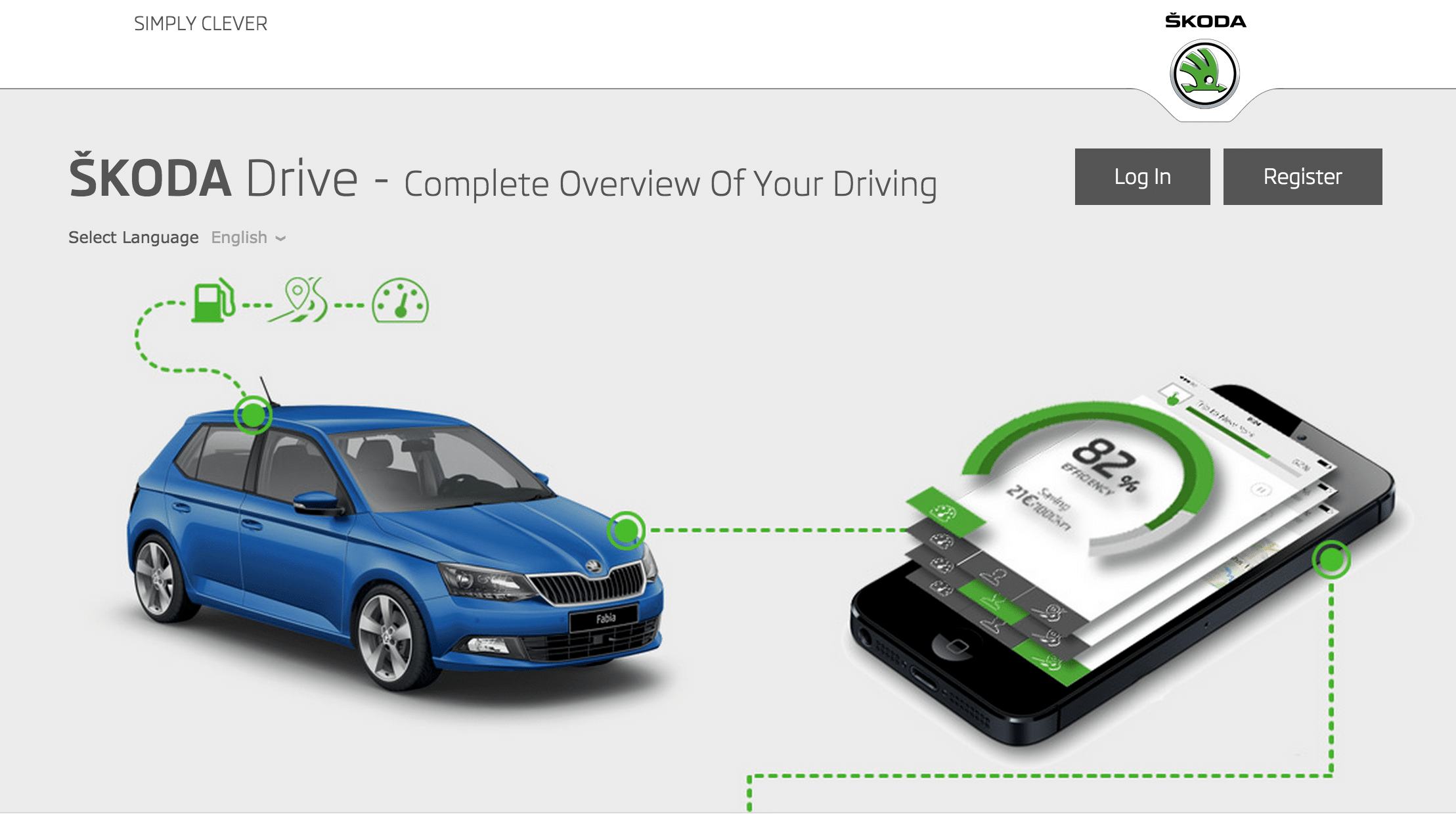
The latest news comes from the security firm Trend Micro, which wrote today about a vulnerability in SmartGate, a connected car technology deployed in vehicles by Volkswagen’s Czech subsidiary Škoda Auto. Part of Škoda’s Fabia III cars, SmartGate provides a way to read performance information on your car from a smartphone, including data on fuel consumption, maintenance and so on. The cars sell in Europe with model names that include “Fabia,” “Octavia,” “Yeti” and “Superb.”
According to Trend, researchers studying SmartGate discovered that the system does a poor job of securing data. An attacker can read more than twenty parameters from the vehicle, assuming she is within range (around 50 feet) and can connect to the vehicle’s on-board wi-fi network. Breaking the security on the car’s network is easy, Trend said, because the vehicles use Wi-Fi Direct technology to make connecting to it more seamless and both the Wi-Fi password and Wi-Fi Direct PIN are default values that are published in each owner’s manual.
In a real world test, Trend Micro researchers were able to crack the vehicle’s on board wi-fi from a trailing car, with both vehicles moving. By cracking the wi-fi security, an attacker can collect information on the vehicle’s occupant and, possibly, even lock them out of the on board wireless access point.
Škoda Auto did not respond to a request for comment on the Trend research prior to publication.
Trend notes that the problems with Škoda SmartGate are more of a privacy- than a security and safety concern. However, if the research conducted by Chris Valasek and Charlie Miller is any indication, determined attackers may be able to use weaknesses in the access point to pivot to other systems communicating over the CAN (controller area network). In the research published last week, attacks on critical systems on a Fiat Chrysler Jeep Cherokee were preceded by a compromise of the Chrysler UConnect system, which controls onboard media and entertainment systems.
Trend recommends all owners of Škoda cars that support SmartGate change the Wi-Fi transmission (Wi-Fi TX) power to 10% and change the default Wi-Fi password, Wi-Fi Direct PIN (if Wi-Fi Direct is supported) and the Wi-Fi network name.
Fiat Chrysler recalled 1.4 million late- model vehicles last week after revelations about vulnerabilities in the UConnect technology and possible attacks on critical on board systems. In a blog post on Friday, the company said it is expanding the recall of vehicles to apply a software security update beyond what the company initially indicated. RAM pickups, Jeep Cherokee and Grand Cherokee SUVs, Dodge Challenger sports coupes and Viper supercars are included in the recall.
Also last week, the firm NCC Group of Manchester, England demonstrated what it claims are vulnerabilities in several car infotainment systems that it says could “potentially put lives at risk,” according to a published report. NCC researchers discovered a method for sending data to infotainment systems via digital audio broadcasting (DAB) radio signals and compromising those systems. NCC’s research director, Andy Davis, said that the DAB attacks – which have only been tested in a lab environment – could conceivably be used to compromise many vehicles within broadcast range simultaneously. He likewise warned that attackers who compromised the infotainment systems could pivot to attack critical systems, as Valasek and Miller demonstrated.
Trend said that Volkswagen and Škoda Auto should strongly encourage new owners to change the default password and PIN that ship with their vehicles and dial down the range of the in-car wi-fi to 10% so that remote attackers can’t get easy access to the vehicle network. The car maker should also consider a physical on/off switch for the wireless network so that it is not on by default whenever the car’s ignition is on.
“There are two issues that have to be addressed, development of new cars with fewer vulnerabilities and automated vulnerability analysis of existing cars”, says Chip Block, Vice President of Evolver, a firm that develops applications used by automotive companies for managing the sales and maintenance tracking. Block believes that car makers will need to build response to software-based issues into their current recall process.
“Rapid analysis, by mechanic level people, of existing cars will be essential for regular maintenance and recall response,” he said in an e-mail statement.

Pingback: Endnu et bilmærke dumper it-crashtest: Skoda-wifi kan aflyttes og kapres - Zyberdata