In-brief: The FBI seized equipment from noted security researcher Chris Roberts on Wednesday, alleging that Roberts may have tampered with the systems aboard a United flight to Chicago. Roberts denies the claim.
Chris Roberts (a.k.a sidragon1), a leading researcher delving into the security of airplanes, was pulled off a plane in Syracuse, New York, on Wednesday by the FBI and questioned, apparently over concerns that he attempted to hack into critical systems aboard a United flight earlier in the day. [Updated to add comments from Mark Rasch. 4/17/2015 11:20]
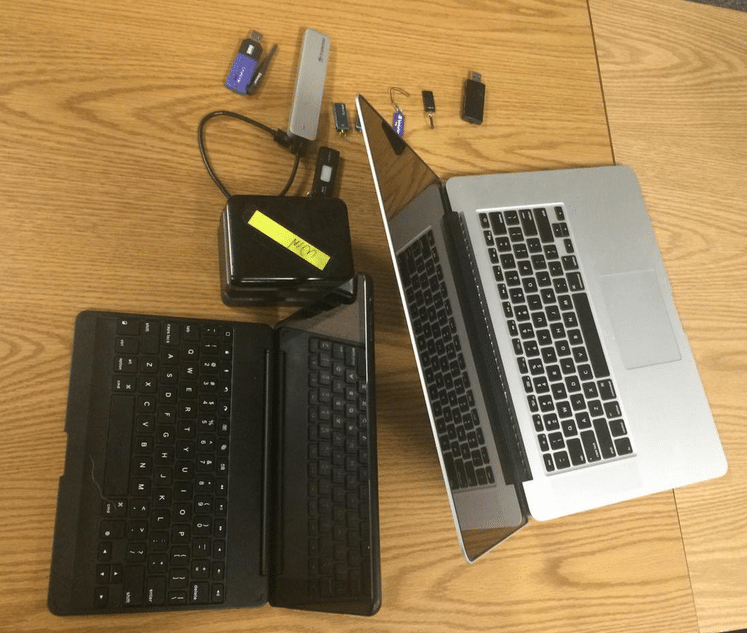
In an interview with The Security Ledger on Thursday, Roberts said that he was questioned by FBI agents for four hours Wednesday evening and then released. (A text message conversation, however, suggests he was detained for around two hours.) His laptop and a variety of external storage devices were confiscated by the FBI, which said it wanted to determine whether Roberts, an authority on security vulnerabilities in modern aircraft, may have accessed sensitive systems on a flight from Colorado to Chicago earlier in the day.
Roberts is the founder and Chief Technology Officer of One World Labs, a security research firm.
In response to mentions of his earlier research on Twitter, Roberts, using the @sidragon1 handle, had tweeted about his ability to hack into in-cabin control systems on the Boeing 737.
“Find myself on a 737/800, lets see Box-IFE-ICE-SATCOM, ? Shall we start playing with EICAS messages? “PASS OXYGEN ON” Anyone ? :)”
EICAS refers to the Engine Indicating and Crew Alerting System, critical in-flight systems.
That apparently got the attention of federal authorities, who were waiting for Roberts when he arrived in Syracuse that evening for a scheduled talk – ironically, to an audience made up of law enforcement.
“Two officers got on, two regular Syracuse PD. They walked back there, and past me. The FBI agents walked on, they walked past me and turned around at which point, I said ‘so, should I get my bags now?’ and they said ‘yes, please, Mr. Roberts,” he told Security Ledger on Thursday.
Roberts has been demonstrating vulnerabilities in the avionics systems used on modern airplanes for the past five years, warning that modern planes have converged critical systems and non-critical systems such as in-flight entertainment and wi-fi in ways that create serious security and safety risks.
He isn’t alone. Ruben Santamarta a Principal Security Consultant for the firm IOActive demonstrated at the 2014 Black Hat Briefings how satellite based communications devices (SatCom) used to provide Internet access to planes in flight could be used to gain access to cockpit based avionics equipment. Brad “RenderMan” Haines has also demonstrated methods for moving from in-flight entertainment systems to critical control systems aboard planes.
Roberts said he had met with the Denver office of the FBI two months ago and was asked to back off from his research on avionics – a request he said he agreed to. But recent weeks have seen him get high profile media attention from Fox news and CNN, who ran stories about the danger of hacking into airplanes in flight.
Those stories apparently got the attention of federal authorities, Roberts said.
“I don’t know what the logic is. They’re probably pissed that FOX picked up on it and CNN picked up on it and it’s gotten a lot more media attention,” Roberts said.
“This has been a known issue for 4 or 5 years where a bunch of us has stood up and pounded our chest and said this is an issue…Are they pissed because there are credible threats and we’re giving those credible threats more intelligence, or because we’re standing up and saying ‘there’s a problem,’ or because they can’t get anywhere with this? I don’t know.”
He described a testy but polite meeting with FBI agents, who accused him of “tampering” with systems on a United flight to Chicago. They requested that Roberts unlock his work laptop and provide a password needed to decrypt the hard drive so they could do a forensic analysis of the hard drive. Roberts says he refused the request because of proprietary information stored on the hard drive. He demanded a warrant to search the computers and hard drives. Roberts indicated via Twitter that he had not received a warrant nor had his equipment been returned.
Amanda Cox, a spokeswoman for the Albany division of the FBI declined to comment.
Mark Rasch, a former Department of Justice Lawyer and now head of Rasch Technology and Cyberlaw said that Roberts’s tweet was “borderline” and that the FBI would almost certainly obtain a warrant to search the devices. Still, he questioned why the agency was following the social media posts of a security researcher closely enough to track down his flight in real time and apprehend him.
“If this guy is going on Fox and CNN and talking about this, they know for certain that he is not a threat,” Rasch said.
Roberts says the real issue is not his research, but the failure of firms like Boeing and Airbus to respond to issues raised by security researchers. Roberts said the airline manufacturers hadn’t learned the lessons of technologies companies like Cisco and Microsoft about the proper response to responsible disclosure by security researchers.
“It feels like this industry is going through the same issues. The problem is, if I break a F5 device or a Cisco device, I’m not harming anybody. I screw around with an airplane, I’m taking 100 to 400 people out of the sky and you’re not recovering from that.”
The FAA and authorities should be taking a more assertive stand in forcing airlines to address known security issues he said.
