In-brief: A new and sophisticated ransomware family dubbed “Fessleak” is spreading in malicious advertising (or “malvertising”) campaigns by exploiting newly disclosed flaws in Adobe’s Flash technology.
Security researchers are warning of a new and sophisticated ransomware family, dubbed “Fessleak” that is spreading in malicious advertising (or “malvertising”) campaigns – in part by exploiting newly disclosed flaws in Adobe’s Flash technology.
In a blog post on Thursday, Invincea said that malicious advertisements appearing on high-traffic websites have been linked to the new ransomware. Sites from which malicious advertisements have been served include Huffingtonpost.com, Photobucket.com and RT.com, the Russian news website.
Once infected by Fessleak, computers have their hard drive’s contents encrypted until owners pay a ransom.
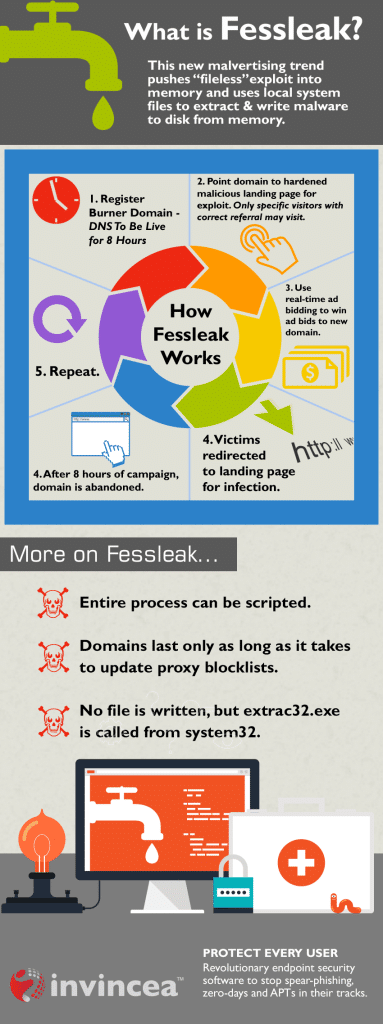
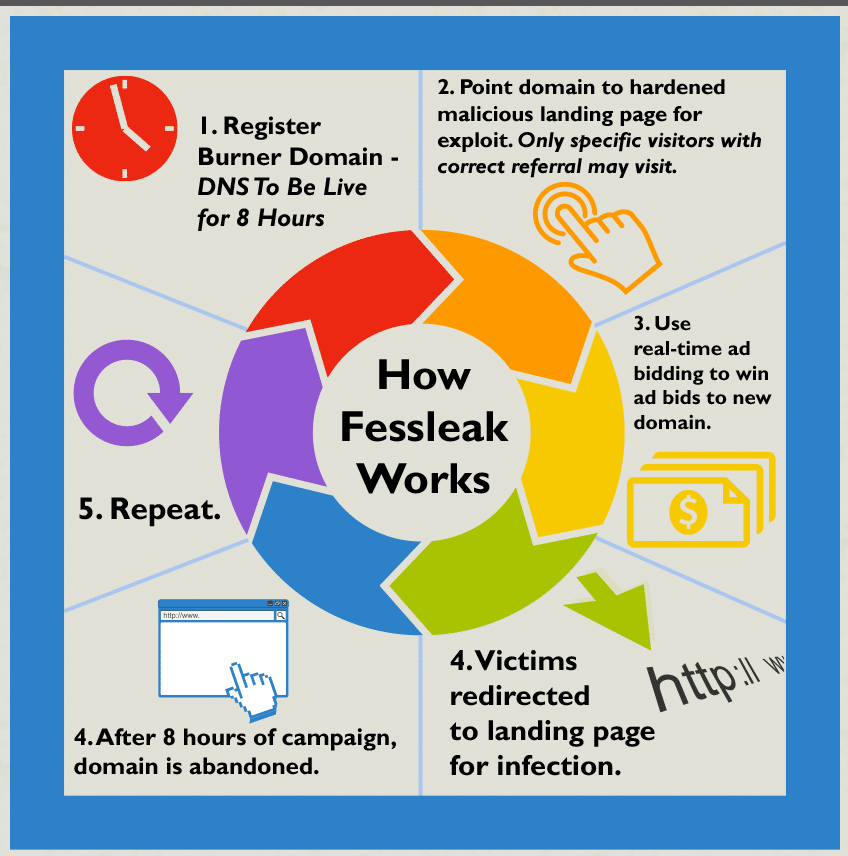
According to Invincea*, FessLeak is an example of a new trend in the ransomware space: the use of file-less (Adobe) Flash malvertising. Unlike traditional “dropper” attacks, in which a malicious file is pushed from infected websites, in “file-less” attacks there is no dropped file. Instead, the malware is loaded into system memory and then extracted by taking advantage of programs that are already running on the infected computer, specifically: the local System32 file, extrac32.exe.
[Read more Security Ledger coverage of ransomware here.]
Invincea notes that the FessLeak malware is also able to detect the presence of virtual containers that are used by security researchers and some endpoint protection products to isolate and analyze malicious or suspicious programs. When FessLeak detects that it in a virtual container, it is programmed to quit, denying researchers the opportunity to study it.
However, the a spate of critical and remotely exploitable vulnerabilities in Adobe Flash in recent weeks has prompted the Fessleak authors to switch methods: exploiting Adobe 0-Day vulnerabilities like CVE-2015-0311 to deliver the malicious payload rather than using the “file-less” infection method. That follows adoption of the Adobe exploits by prominent exploit kits and other malware families including the Angler exploit kit and the Reveton. It may also be a response to a recent patch by Microsoft (MS15-004) that closed a directory traversal vulnerability on Windows that was being leveraged in the file-less attacks.
Invincea adopted the name “Fessleak” after studying “WhoIs” domain registration records for the short-lived web domains used to push the Fessleak malware. Invincea has observed “dozens” of these domains, most of which are active for only a few hours before going dark.
