In-brief: adoption of Internet of Things technologies puts a premium on the use of network segmentation to ensure connected devices don’t undermine the overall security of the network, according to Cisco’s Scott Harrell.
I’m speaking on a frequent (and increasing) basis with customers about the opportunities and risks that they need to prepare for as they continue to support new business models related to mobility, cloud and the Internet of Things (IoT).

In many instances, my discussions with customers turn to the need for cybersecurity. Security models will need to radically change in order to provide the right level of protection for this new, connected world. One crucial aspect that I often encourage practitioners to think differently about is network segmentation.
In the early days of networking, a primary goal was merely to connect systems within an environment and between disparate locations. These networks and their components extended to wherever employees and data were located. But these first generation networks were often implemented in a flat and unsegmented way.
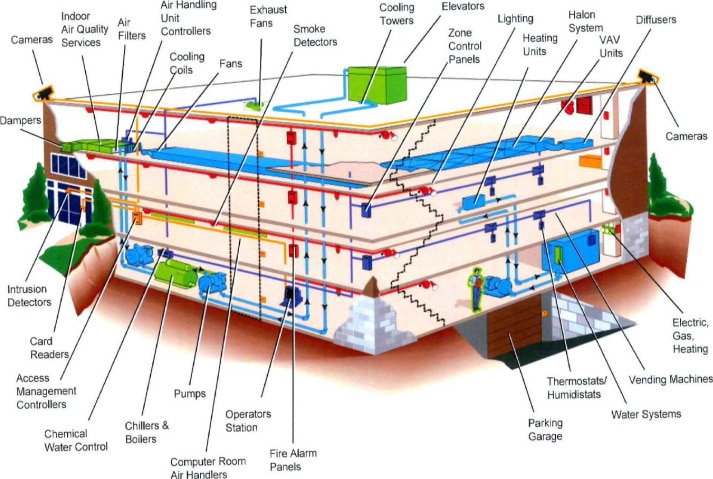
As networks grew and expanded, new devices and applications with widely varying security postures were connected to them. Today, this includes mobile devices, web-enabled and mobile applications, hypervisors, social media, web browsers, and home computers. These devices expand the attack surface of networks and creates opportunities for attackers to compromise non-critical assets and pivot from there to attack more critical assets and data.
Modern networks extend even farther and comprise data centers, endpoints, virtual, mobile, and the cloud. As adoption of IoT strategies evolves, security and network practitioners must rethink how the resources on their network are separated and improper or malicious communications between resources can be limited or disallowed.
This kind of segmentation is imperative to ensure that highly secure access is consistently maintained. Proper policies must be applied to protect valuable business data and intellectual property, limit the lateral spread of malware and inhibit reconnaissance.
Having the right approach in place to segregate valuable network resources enables security practitioners to establish policies that allow only designated users to access sensitive information for specific applications, servers, and network resources. In fact, applying proper network segmentation can make it much more challenging for an attacker to locate and gain access to valuable information. In some cases, when an attack is underway, segmentation can be used to provide dynamic controls to contain a network intrusion and limit the damage from an incident.
To illustrate how this might be applied in a real world setting, imagine the implications for a hospital or health care environment. In such an environment, segmentation is crucial. Clinical staff need uninterrupted access to critical tools like IV pumps, respirators and patient monitoring systems. At the same time, patients seeking care at the hospital want to enjoy Internet-enabled games and other forms of entertainment during their hospital stay. Segmentation makes sure that a savvy patient playing an Internet game on their smart phone or laptop can’t also access patient records or disrupt the operation of a life-sustaining device in an adjacent room.
For organizations embracing technology transitions such as IoT, cloud and mobility, now is the time to revisit and evolve existing network designs that have been in place for years. The technology is available today to apply segmentation strategies that enable you to apply these innovations and maintain a strong security posture. For example, administrators can create policies that de-couple access entitlements from IP addresses. This means that practitioners can establish common access policies that are role-based and that dynamically segment access. This is a far simpler approach than using multiple virtual LANs (or vLANs) to manage users’ access and then copying complicated access control lists across the network.
Today there are 10 billion connected devices but that number is expected to grow exponentially – exceeding 50 billion sensors, objects, and other connected “things” by the year 2020.
Unfortunately, attackers don’t discriminate. Their motives and persistence have increased along with their understanding of new technology and its applications. That means that the number and variety of attacks will likewise increase as we continue to connect previously unconnected objects and devices to the Internet. To capitalize on the vast opportunities that the IoT represents, we must take steps now to apply network segmentation policies that can keep pace with the growth and diversity of the modern network.

The so called “internet of things” is never gonna happen, at least not at my home! NEVER in a million years would I buy appliences that need to be connected to the internet to work, or want an internet connection to send data collected about me anywhere!
The Internet of Things is already happening, although the consumer home market is only a small part of it. Factories, construction sites, office buildings, power plants, hospitals, etc., are all getting connected things. You might never want an Internet-connected home appliance (neither do I), but they do not “need to be connected” to the Internet to work. In any case, the cable TV box in your living room and the electric meter on the side of your home are already part of the Internet of Things.
Pingback: Links 31/1/2015: Open Lunchbox, Librem 15 at Around $400,000 | Techrights