Visibility is surprisingly tricky. The security industry offers many disparate tools to provide customers “visibility” into what is happening on their networks. Among them are tools that track what applications are on the network, tools for enumerating and tracking software vulnerabilities, tools for determining when sensitive data has left a network, tools that indicate when attacks are underway and tools that identify and analyze network data flows – to name just a few.

Of course, layered on top of all this “visibility” are further systems that correlate and analyze what the mission-specific tools are seeing. Promises of a “single pane of glass” aside, the result is often a mishmash of data and events that require skilled security practitioners to analyze and interpret. The mishmash, in turn, leads to errors in analysis and prioritization.
Albert Einstein famously said “Any fool can know. The point is to understand.” So it is in the information security industry, where a common refrain is “you can’t protect what you can’t see.” Given the rise in complexity and the exponential increase in what must be protected, however, we might take our queue from Einstein and change our mantra from “you can’t protect what you can’t see” to “you can’t protect what you don’t understand.”
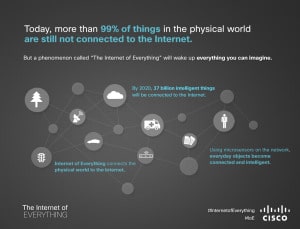
But its also true that understanding – in the context of information technology – is becoming more difficult to attain. There are already 10 billion connected devices in the world. And already a lack of in-depth visibility into extended enterprise networks means that knowledgeable attackers have plenty of hiding places and a growing supply of tools that can subvert legacy defenses. And Cisco predicts that those 10 billion devices will grow rapidly – exceeding 50 billion sensors, objects and other connected things by the end of the decade. The vast majority of these will be what are currently considered ‘non-traditional’ endpoints.
At the same time, the diversity of software applications available to users is growing exponentially via SaaS and other application trends. Finally, it is often noted that with the adoption of IPv6 there will now be more IP addresses (3.4×1038) than stars in the universe – and that by an order of magnitude.
All this diversity will strain legacy security technologies and defense-in-depth approaches to the breaking point. Solutions that operate in isolation and make decisions based only on incomplete or inferior data will have diminishing value to organizations.
My point? For information security professionals to be able to do their job, it is essential for the next-generation security tools and systems to deliver visibility. And by “visibility” I mean full contextual awareness of both physical and virtual hosts, operating systems, applications, services protocols, users, geolocation information, content, network behavior, threats, and malware. This also means these systems must rapidly evolve to be more open and be able to ingest and then share contextual information from a variety of sources.
This means that vendors must abandon silos and walled gardens, focusing on bridging competitive boundaries and enabling their disparate systems to work seamlessly with a broad ecosystem of third party solutions. Common APIs based on industry standards are needed to bridge those gaps.
Next-generation systems must have the ability to correlate security events and alerts within this rich environment automatically. Security talent is in short supply and overtaxed. Security tools must pick up the slack with more and better automation of what are now manual tasks: enabling the operator to quickly see all of their security events and understand the relative importance and priority of each.
Finally, visibility and correlation must expand to cover key control points and a wider diversity of endpoints, providing full understanding of malicious incidents from their inception and enabling security professionals to quickly assess and contain those events in near real-time.
As our computing environment becomes large, more complex and more integrated with our physical world, protecting enterprise environments will demand new strategies and new tools to enable understanding, prioritization, and automation across dynamically changing environments. This evolution will enable enterprises to compress the time from initial detection to containment for an enterprise’s most significant threats.