Microsoft Corp. has taken action against yet another cyber crime network, taking control of- and shutting down a managed DNS (domain name system) operated by the firm No-IP that were being abused by cyber criminals, the company said on Monday.
The domains were associated with malware families named Jenxcus and Bladabindi that are believed to have infected on some 7.5 million systems, globally.
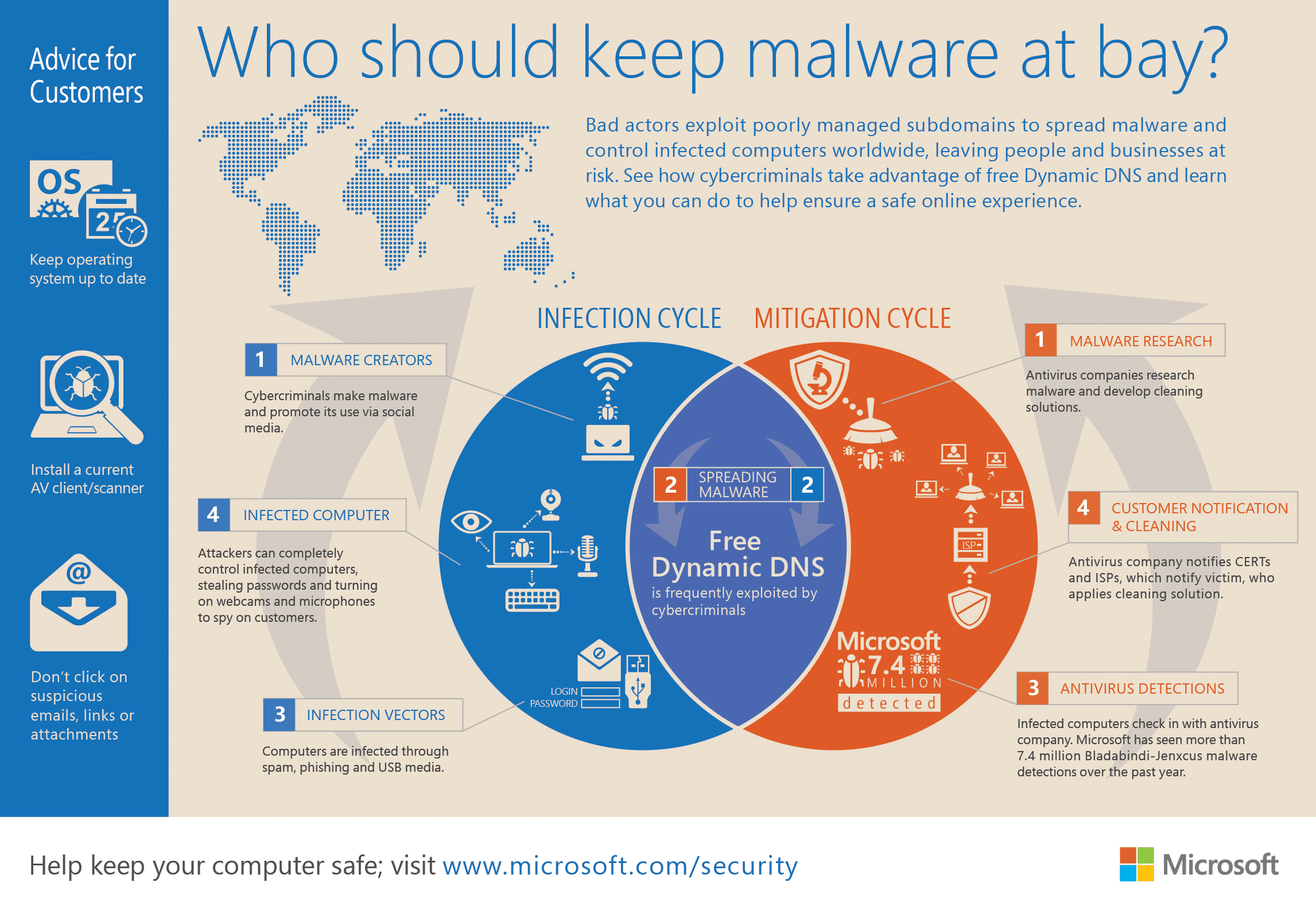
The malicious programs – which are used to spy on the operators of infected systems – use Dynamic DNS services like NO-IP to communicate with command and control systems used to manage infected systems. Dynamic DNS makes the malicious systems more difficult to trace.
In a post on Microsoft’s Digital Crimes Unit blog, Richard Domingues Boscovich, the company’s Assistant General Counsel said that the company had filed a civil case on June 19 naming two foreign nationals: Mohamed Benabdellah and Naser Al Mutairi along with a U.S. company, Vitalwerks Internet Solutions, LLC (doing business as No-IP.com), for “their roles in creating, controlling, and assisting in infecting millions of computers with malicious software.” The suit alleges that the collective actions of Vitalwerks and the two men harmed Microsoft, its customers and the public at large.
“We’re taking No-IP to task as the owner of infrastructure frequently exploited by cybercriminals to infect innocent victims with the Bladabindi (NJrat) and Jenxcus (NJw0rm) family of malware,” Boscovich said.
No-IP is described as a global managed DNS service that was a mainstay of malicious software campaigns. According to Microsoft’s Digital Crime Unit (DCU), No-IP domains are used by 245 different types of malware. And they were behind 93% of all the infections linked to the malware families Bladabindi and Jenxcus.
Microsoft said it has detected more than 7.4 million Bladabindi-Jenxcus detections over the past 12 months – a figure that doesn’t include detections by other anti-virus providers.
In a companion post on the blog of Microsoft’s Malware Protection Center (MPC), researchers Tanmay Ganacharya and Francis Tan Seng wrote that the MPC has seen a steady increase in infections linked to Bladabindi-Jenxcus in recent months – often as a result of malicious web sites or e-mail based attacks. The malware can install backdoor trojans on infected computers and spy on users: taking snapshots and recording videos of activity on the infected host.
The individuals named in the case are depicted as Internet dead beats: ignoring reports by the security community regarding abuse on domains it managed.
“Despite numerous reports by the security community on No-IP domain abuse, the company has not taken sufficient steps to correct, remedy, prevent or control the abuse or help keep its domains safe from malicious activity,” Boscovich said.
Read: Microsoft Takes On Global Cybercrime Epidemic in Tenth Malware Disruption.