As camera-equipped mobile phones have proliferated in recent years, CNN pioneered the crowd sourcing of news with its highly successful and much-imitated iReport program. But aspiring iReporters would do well to hold off submitting their stories using CNN’s mobile application for the iPhone – at least for a few days.
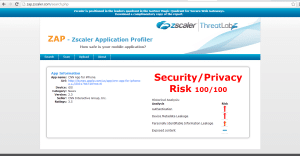
According to a report from the security firm zScaler, the CNN App for iPhone fails a basic security test: failing to encrypt traffic sent to and from the application, including a user’s login and password.
The flaw, which was only found in the CNN App for iPhone, could allow an iReporter’s account to be compromised, giving strangers access to any stories they have submitted to the news network.
CNN senior director of public relations Matt Dornic acknowledged the flaws and said that CNN has updated the application and will be submitting it to Apple as soon as possible.
According to a zScaler blog post, the current CNN for iPhone App, Version 2.30 (Build 4948), sends passwords in clear text. According to zScaler, which observed the behavior using its ZAP tool, a network traffic sniffer, the password is exposed when a user first creates their iReport account and during any subsequent logins to the application.
[Read more Security Ledger coverage of mobile security here.]
Mobile applications that send passwords in the clear aren’t so unusual, said Michael Sutton, the Vice President of Security Research at zScaler. According to data from zScaler, around 10 percent of mobile applications expose sensitive information in some way: either by failing to encrypt it, or using inadequate encryption that can easily be broken.
However, zScaler felt that the CNN mobile application raised the bar because of its popularity, and because the app includes features to allow citizen reporters to upload photos and other material to CNN’s iReport section.
Sutton said that most mobile applications – like CNN’s – are essentially small web browsers that communicate using HTTP and secure HTTP. As a result, they suffer from many of the same security and privacy weaknesses as general purpose browsers.
“It’s frighteningly common that you find apps that do not have adequate security,” he said. Sometimes that is the result of weak processes – like having different teams our outside contractors responsible for building mobile applications.
In the case of CNN, zScaler researchers found that both initial account setup transmissions and subsequent sessions were sent in clear text (HTTP). In traffic captured by zScaler, the account password (p@ssword) was shown being sent unencrypted, along with all other registration and login information.
“The concern here is that anyone on the same network as the user could easily sniff the victim’s password and access their account. Once obtained, the attacker could access the iReport account of the user and compromise their anonymity.”
The frequent practice of reusing passwords means the same credentials could potentially be used to access other online services the user frequented, Sutton said.
However, weak security did not extend to the CNN’s mobile application for the Android platform. To the contrary: that mobile application sets a high bar for security, using SSL security for all communications and pinning the SSL servers to prevent sessions from being hijacked.
The reasons for the differences between the two applications are not clear. The application was updated on July 11th, prior to zScaler registering its complaint with CNN. Dornic of CNN suggested that the Android version of the CNN mobile application may be of more recent vintage.
He said CNN would urge Apple to quickly approve their update so that it could be made available to users via the iTunes App Store.
Sutton said that Google and Apple could do more to vet mobile applications for the kind of weak security his team discovered in the CNN application.
Those companies do a good job of weeding out malicious applications and those that violate their own program guidelines or the guidelines in place for their application marketplaces. However, neither Apple nor Google look for software vulnerabilities or poor coding practices in submitted applications.

This is akin to stating that WiFi and GSM both leak passwords because anyone around you could be using a rogue access point or IMSI catcher that your phone could automatically connect to without you ever even knowing. Majority of Internet users of the world probably send their POP3/IMAP email credentials over non-SSL too.