The firm Duo Security* said that it has discovered a vulnerability that affects a range of two-factor authentication plugins for the WordPress content management platform. The vulnerability could allow a malicious insider to use credentials for one WordPress site to log into a different site that is part of a ‘multi-site’ WordPress deployment without needing to pass a multi-factor authentication test.
In a blog post on Thursday, DUO co-founder and CTO Jon Oberheide said that the vulnerability was discovered as part of an internal review of DUO’s two factor WordPress plugin, but that researchers realized it affects at least two other multi-factor plugins.
DUO issued a warning to users of its plugin. The company also reached out to WordPress and to the publishers of other multi factor authentication plugins to address the issue, Oberheide wrote.
DUO makes multi-factor authentication technology that allows users to log-in using a combination of username, a traditional password and a second factor such as a mobile device or a one-time password.
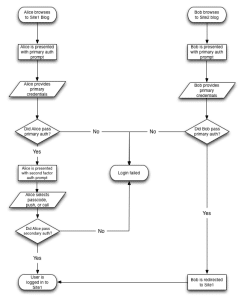
According to the company, the vulnerability only affects so-called “multisite” deployments where more than one WordPress site has been grouped under the same DUO account, but the DUO plugin has been enabled on an individual per-site basis. The vulnerability allows a user of one site of a multisite WordPress deployment to bypass the second factor of authentication when logging onto another site.
WordPress sites that use Duo, but are not part of multi-site deployments aren’t affected by the vulnerability. Furthermore, the bug only allows an attacker to bypass the second factor login. She would still need to have a valid user name and password for accounts at both sites to gain access, DUO said.
(*) Editor’s note: DUO Security is a paying sponsor of The Security Ledger.

For those who may come across this, we have an updated release that addresses this issue and details on the fix, https://www.duosecurity.com/blog/duo-securitys-wordpress-plugin-updated-to-address-multisite-vulnerability