A new endpoint security startup, Confer, pulled the covers off its technology on Wednesday, announcing a new services-based endpoint protection product that it claims will provide better protection against malicious software and advanced attacks.

Based in Waltham, Massachusetts, Confer has been in existence for just over a year and has received $8 million in venture funding from North Bridge Capital and Matrix Partners. The company’s cloud- and endpoint-based software enables organizations to collaborate to stop sophisticated attacks by sharing attack and malware anonymously with other Confer customers. The company said its technology will appeal to enterprise customers who have grown weary of malware infections that manage to bypass or elude traditional anti virus software.
Confer is just the latest company to see dollar signs in corporations’ waning enthusiasm for anti malware software. Modern anti malware products are still focused on securing Windows endpoints. They are geared for use in the enterprise are typically large and resource-intensive suites that encompass functions like desktop firewall, antivirus, host intrusion prevention, anti-spam, data leak protection and other features. A number of studies and assessments suggest that those suites are ineffective in spotting and blocking new malicious code outbreaks. Despite that, antivirus software still accounts for the lion’s share of IT security spending at organizations of all sizes.
[Read more Security Ledger coverage of Advanced Persistent Threats.]
“The endpoint is more important today than ever,” said Paul Morville, Confer’s Vice President of Products. “We operate in a more distributed environment. That means the endpoint is both the first and last line of defense.”

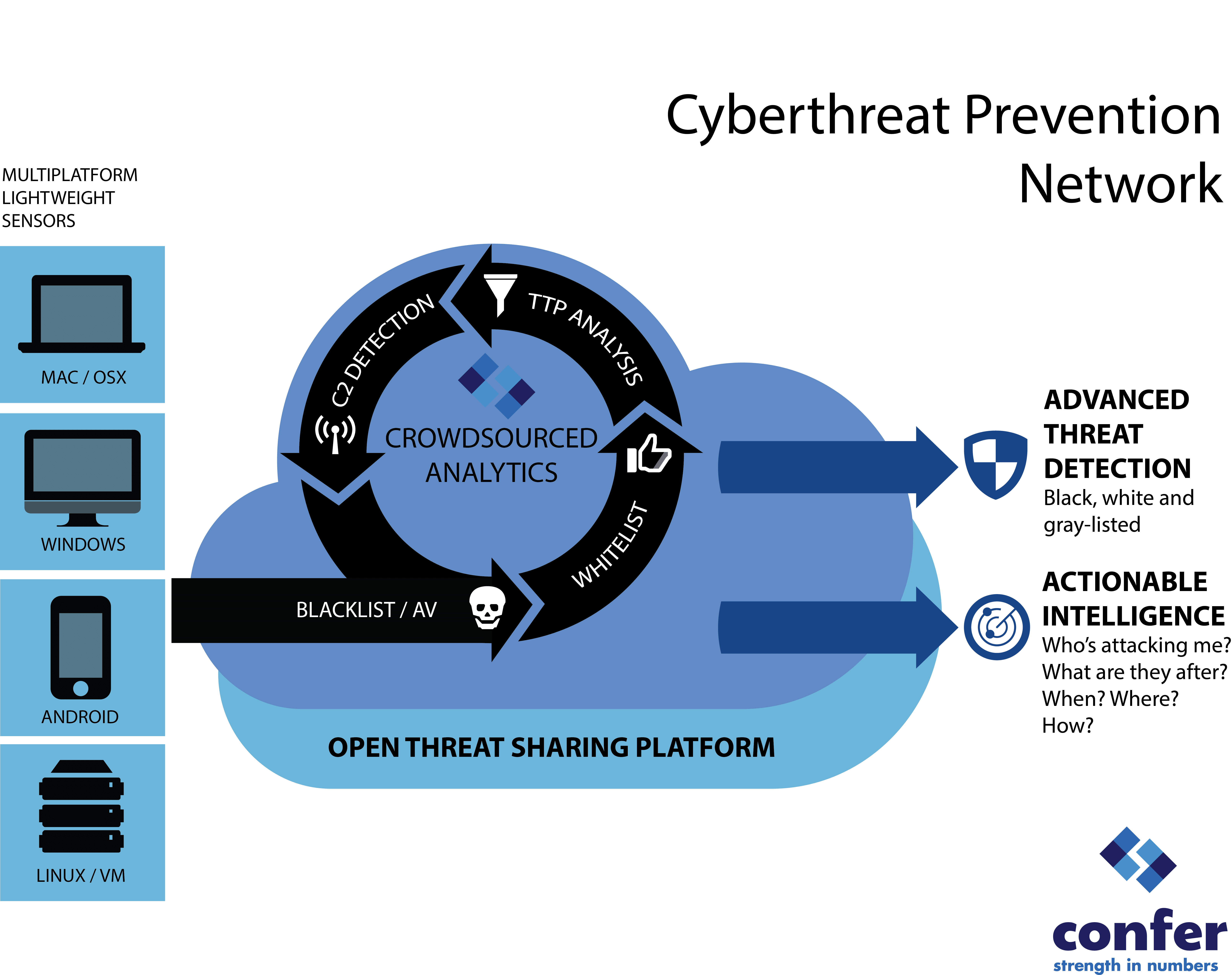
As an alternative, Confer combines a small agent for Windows, OS X and Android endpoints with cloud-based intelligence services that correlate activity on the endpoint, looking for “tactics, techniques and procedures” used by malicious actors, said Jeff Kraemer, Confer’s Chief Technology Officer. Those indicators could include the presence of any new executable code or components that may be linked to a malicious infection -things like library calls or unusual patterns of accessing files. A small sensor on the endpoint sends that data to Confer’s cloud-based backend system for analysis. There, the company checks the information against massive white- and blacklists, runs any executables through 40 different anti malware engines and observes grey list applications running to see if they behave suspiciously (keystroke logging or connecting to command and control infrastructure).
Plenty of traditional anti-virus vendors have switched to a “cloud-based intelligence” model within the last five years, also. But Confer’s executives say they’re different, describing Confer as a “community-based solution that shares information about threats.” Some of that is about gathering analyzes suspicious activity from across the Confer user base. But Confer is also tapping into open-source platforms like MITRE’s STIX and TAXII threat data sharing standards. That will allow it to interoperate and exchange data with other similarly compliant systems, according to Morville.
He said Confer is just making the kinds of analysis that wealthy and sophisticated firms do available to a much wider audience.
“What I see happening is that, at the high end, people aren’t relying exclusively on vendors for data. They’re doing their own analysis or engaging with FS-ISAC (the Financial Services Information Sharing and Analysis Center) to get other sources of intelligence.”
Morville thinks there is demand for products that are architected to do that kind of data sharing natively. “We in the security industry are guilty of asking people for their watch in order to tell them what time it is,” he joked.
Confer also promises to provide context around malicious activity – not just whether an infection happened, but where that malware came from, when the initial infection happened and what actions the malicious software took after it was infected.
“We answer questions about where your’e being attacked and who is being attacked,” Morville said.
A lot of the light and heat in the endpoint protection space these days is on advanced and targeted threat detection – much of it leveraging cloud-based data aggregation and analysis. The successful initial public offering of the firm FireEye signaled the viability of “advanced threat detection” as a business. In recent weeks, that company acquired Mandiant, a highly specialized services firm that helps companies investigate and recover from targeted attacks.