A group of security enthusiasts, including some leading figures in the IT security industry, have pledged their hard-earned cash toward a bounty for the first hacker who can fool Apple’s new iPhone 5s Touch ID fingerprint scanner using a fingerprint lifted without the owner’s consent.
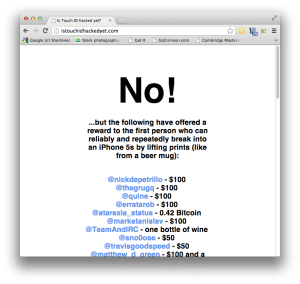
A web site, istouchidhackedyet.com, has been set up to coordinate the campaign, with more than $14,000 in pledges committed (via Twitter posts) from a Who’s Who of the IT security community. The project was the brainchild of Robert David Graham of Errata Security (@ErrataRob) and Nick De Petrillo (@nickdepetrillo) of Crucial Security, who launched the contest and set up the web site to collect donations.
Security luminaries from across the globe chipped in funds to build a bounty, including Travis Goodspeed ($50) and Nick Percoco (@c7five) of the security firm Trustwave ($250). The largest single donation – $10,000 – came by way of Arturas Rosenbacher (@arturas) from the firm IOCapital. Interested parties can sign on to contribute to the crowd-funded project merely by tweeting #istouchidhackedyet.
While the terms of the contest are a bit vague (most were relayed in a series of Tweets from Graham and De Petrillo), organizers have asked for video evidence of the hack, starting with the enrolling of a legitimate print, then the lifting of that print without the owner’s consent (i.e. no molds taken directly from the finger), the creation of a counterfeit print and the successful use of that print to authenticate to the iPhone 5s.
“Enroll print, Place it, lift it, reproduce it, use the reproduction to unlock the phone without being locked out. Video,” De Petrillo tweeted on Wednesday.
Fingerprint scanners have long been known to be susceptible to attacks using forged prints. More than ten years ago, researchers led by Tsutomu Matsumoto at Yokohama National University in Japan conducted a series of tests designed to fool biometric readers more than a decade ago. In a paper published in 2002, the researchers found that gelatin (or “Gummi”) fingers were successful around 80 percent of the time.
Hacking biometric finger scanners was even the subject of an episode of the television show Myth Busters, where producers used a variety of forged prints – including a simple photocopy of a registered fingerprint — to fool fingerprint scanners embedded in a door lock and a laptop computer.
The effectiveness of the biometric depends on the kind of scanner used. Some simply match fingerprint patterns – a highly vulnerable approach. Scanners that use more sophisticated approaches, like capacitive sensors designed to weed out living from inorganic material, as well as optical and ultrasound sensors are more resistant to forgeries.
