Call it “the quantified self” – that intersection of powerful, IP-enabled personal health monitoring tools and (usually) Web based tools for aggregating, analyzing and reporting.
The last five years has brought an explosion in these products. In addition to the long-popular gear like Garmin GPS watches – must have items for the exercise addicted – there’s a whole range of new tools for the merely “exercise curious” or folks interested in losing weight or just figure out what, exactly, they do all day. Count Nike’s FuelBand, Jawbone’s UP, and Fitbit in that category.

Alas, a growing number of reports suggest that, when it comes to medical devices and health monitoring tools, the security of sensitive personal data isn’t a top priority. The latest news comes by way of researchers at Florida International University in Miami, Florida. A team of three researchers, composed of students and faculty, analyzed the Fitbit health monitoring device and found several, exploitable vulnerabilities that could allow malicious hackers to hijack Fitbit users’ accounts, access or even manipulate their personal health data to earn prizes and monetary rewards.
The report, published last month and available for download from Cornell University’s arXiv.org (PDF), found that exploitable holes in the Fitbit device, the companion web-based software and the communications protocol used to exchange data between the two was an example of the “careless integration of health data into social networks” that was “fraught with privacy and security vulnerabilities.”
Fitbit, based in San Francisco, sells a range of wireless personal fitness devices, including Flex, a sleep and activity monitor that is worn as a wristband. The researchers studied Fitbit One, a similar clip-on tracking device that monitors both sleep and activity.
Researchers, Mahmudur Rahman, Bogdan Carbunar, Madhusudan Banik at Florida International’s School of Computing and Information Sciences reverse engineered the Fitbit communication protocol, storage details and operation codes. In the process they identified several exploitable vulnerabilities in the Fitbit software and built FitBite, a suite of tools that exploit these vulnerabilities to launch a wide range of attacks, including eavesdropping, injection and denial of service attacks.
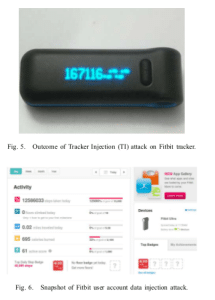
For example, using FitBite, the researchers hijacked the data reported by trackers in their vicinity using a malicious USB base to launch a data injection attack against a FitBit device. The researchers used this attack method to inject the number of steps taken by the “account owner”, while keeping the other values intact. Researchers found that, in addition to being vulnerable to the injection attack, Fitbit’s monitoring software does not check data consistency. A victim account was shown to report a daily total of 12.58 million steps corresponding to 0.02 traveled miles.
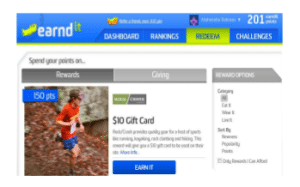
Using the successful injection of large values into Fitbit users’ social networking accounts, the researchers used the FitBite attack tool to achieve special milestones and acquire merit badges, without doing the required work. After injecting 12.5 million steps into a victim account enabled the account owner to acquire a “Top Daily Step” badge. Even more troubling: those rewards can correlate with real world prizes, such as gift cards and financial rewards using services like Earndit, which allow registered users to earn points for each “very active” and “fairly active” minute.
The researchers found that, by keeping their malicious base station running and continuously updating the tracker data (once each 15 minutes), they could bank “fairly active” minutes in an Earndit account linked to the device accumulating “a variety of undeserved rewards” including a $20 gift card.
Other Fitbite attacks include denial of service attack that can prevent users from correctly updating their real-time statistics and battery drain hacks that continuously query vulnerable Fitbit devices.
Fitbit did not respond to a request for comment from The Security Ledger prior to publication of this story.
The security of personal health information stored in IP enabled devices goes well beyond products like Fitbit and Nike’s Fuelband. As The Security Ledger reported, an informal audit of hospital medical devices from major manufacturers, including Philips showed that medical devices have many of the same kinds of software security holes found the devices rife with exploitable security holes, similar to those found in industrial control system (ICS) software from the same firms.

