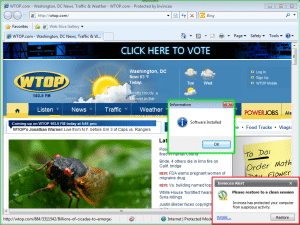
Websites operated by media outlets in the Washington D.C. area were the targets of widespread hacks this week, with web sites for two major radio stations among those found serving up malicious links that installed fake antivirus software on victims’ machines.
Researchers at two security firms, Invincea and zScaler, identified compromises on the web sites of the two stations – WTOP, the D.C. areas largest FM station, and a sister site, FedNewsRadio, 1500 AM, which caters to government employees. The compromises were part of a string of almost identical attacks that redirected visitors to the web sites that push malicious software to victims’ machines. Only visitors using versions of Microsoft’s Internet Explorer web browser were targeted with the attack, zScaler said.
In a related post, researchers at Invincea said the attacks were similar to one they had investigated a breach at dvorak.org, a web site operated by technology blogger John Dvorak. That attack likely was the result of a compromise of WordPress, or a WordPress plugin. It is not known whether the other web sites also used WordPress, a common blogging and content management platform.
That platform and the thousands of add-on modules (or plug-ins) it supports are a common target of attacks. Most recently, users of a popular social media plugin was found to contain malicious code inserted by a rogue contract developer.
The attacks led to web sites installing fake antivirus software identified as FakeAV/Kazy, suggesting that the motives were financial, though the targeting of DC-area web sites could also indicate a state-sponsored (or “APT-style“) attack, as well.

