Medical fraud is a huge issue in the U.S. Depending on whose numbers you use, fraud stemming from false medical claims and reimbursements range from $65 billion a year (a figure generated by the Centers for Medicare and Medicaid Studies) to more than ten times that: $750 billion a year (according to the Institute for Medicine).
To stem the losses, government and law enforcement have been cracking down on fraud. In October, for example, the U.S. Attorney General Eric Holder and Health and Human Services Secretary Kathleen Sebelius announced charges against 91 individuals believed to be behind a huge, interstate Medicare fraud scheme responsible for some $430 million in false billing charges.
Increasingly, though, the U.S. government is turning to technology to help it identify and root out fraud within the system for medical reimbursements. Chief among the ideas under consideration is a beefed up system for identifying health consumers that would replace the use of Social Security Numbers with a cryptographically secure “Smart Card” as a gateway document to accessing Medicare and Medicaid services. With a secure identity document, the thinking goes, the government can be sure that those accessing the system are entitled to receive services.
That’s a nice idea, in theory. But a leading expert on the security of smart cards and medical devices told a House committee on Wednesday that smart card technology is unlikely to stem the most common forms of medical fraud – and could even make medical systems more susceptible to hacking and other online threats.
Kevin Fu, a professor in the Department of Electrical Engineering and Computer Science at the University of Michigan, told the House’s Energy and Commerce Committee on Wednesday that issuing a universal strong ID card to Medicare and Medicaid recipients wouldn’t necessarilly reduce Medicare and Medicaid related fraud, especially if proper care isn’t given to how the ID cards are managed.
Fu, whose past research has exposed security vulnerabilities in contactless smart cards as well as medical devices, told the Committee that a smart card implementation akin to the Department of Defense’s Common Access Cards may be difficult in the context of healthcare.

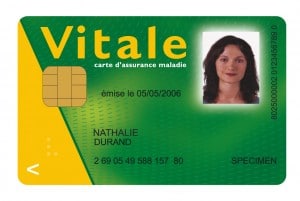
Smart cards have a similar form to ID documents like drivers’ licenses, credit- or ATM cards, but contain a secure, tamper-proof chip that stores sensitive data and can transmit it securely in encrypted form.
In healthcare settings, that chip could include a patient’s identifying information as well as insurance information, health care records and the like. Patients could carry the card with them and physicians throughout the medical system would be set up to take the card, streamlining access to patient information necessary for providing care and accurately billing providers like the Medicare and Medicaid systems.
The government is looking at smart cards as a potent anti-fraud measure that could be used as a unique identifier for both patients and providers, increasing both security and data sharing within the system.
But Fu warned the Committee that smart cards are, themselves, vulnerable to attack and will not be a panacea for many of the most common types of fraud plaguing Medicare and Medicaid.
“Smart cards authenticate smart cards, not people,” Fu told the Committee. “For this reason, a key shortcoming of even the most perfect smart card is the difficulty of securely linking the card with a person. Linking people to a smart card is notoriously difficult.”
In particular, smart cards would do little to protect against fraud in which patients or providers (or both) collude to defraud the system. Smart card systems also present problems in situations in which vulnerable patients are in the care of home health aides.
“A home health care patient who cannot remember to eat breakfast on his own is not going to be able to remember a PIN or password,” Fu told the Committee. “A home health care patient depends greatly on the kindness of others, and can be particularly vulnerable to overly trusting a provider.”
Countries that use smart cards to secure patient records, including the UK, France and Taiwan have struggled with collusive fraud even after smart cards were deployed. Those schemes could be as simple as a legitimate beneficiary sharing their card with another, uninsured individual, or rings of providers and patients colluding with each other to defraud the system.
Finally, Fu noted that relying on a common card infrastructure to link patients and providers could create the conditions for more widespread malware infections within health care organizations.
There are already proven examples of malware spreading from chip and PIN systems, such as payment terminals, to infect back end systems. The same attacks could be leveraged against health care computing systems, then used to manipulate or steal sensitive medical and health information, Fu warned.
While not discouraging the adoption of smart cards, Fu said that the government should ask hard questions of smart card vendors and those supporting a CAC-style card for use with government-supported health care systems. Among them: what controls are in place to prevent card holders from sharing their card with others, and what impact would the extra security procedures have on delivery of patient care?
The government should also anticipate (and budget for) the need to pay to replace smart cards that become compromised in a security breach – and possibly large quantities of the cards and clarify who is liable for patients harmed as a direct- or indirect result of malware infections, Fu said.

Dr. Fu is correct in that this solution will do little to prevent certain frauds. The entire premise of these costly cards and solutions is that the person carrying the card will be most likely to commit the fraud. Since it is the providers, and not the card carriers, who receive the money from Medicare in particular, many of these solutions solve the wrong problem.
The issue of card sharing has been proven to be a red herring, and there are simpler and cheaper ways to verify identity. Our leaders just have to ask a simple question: If nearly all America’s seniors are eligible for Medicare, why would a senior need to borrow a Medicare card? Smart cards developed for the military are designed to protect sensitive locations from intrusion in government-controlled facilities. Here, we have private facilities and we are not trying to stop intrusions